Google has shared some data on the adoption of Transport Layer Security (TLS) by Android applications and it seems that significant progress has been made over the past two years.
According to Google, 80% of Android apps now encrypt traffic by default and the percentage is even higher in the case of applications designed for the latest versions of the operating system. The company says 90% of Android apps designed to run on Android 9 and higher encrypt traffic by default.
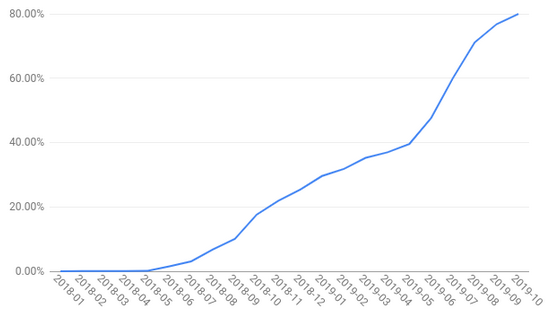
Starting with November 1, 2019, Google has been requiring all apps, including new apps released on Google Play and updates to existing applications, to target Android 9 or higher. The company expects that this too will have a positive impact and TLS adoption rates will continue to increase.
The Network Security Configuration, which Google introduced in 2016, allows developers to configure their app’s network security policy via a configuration file. This policy is automatically configured to prevent unencrypted traffic for every domain in the case of apps targeting Android 9 or 10.
Google is also alerting developers via the Android Studio development environment and the Play Console pre-launch reports when their application allows unencrypted traffic or it accepts user-specified certificates. Both of these practices make it possible to intercept or modify data associated with the application.
If needed, developers can add exceptions to the security policy to allow unencrypted traffic and they can accept user-specified certificates, but Google has advised them to keep the security and privacy implications in mind when doing so.
Related: Google Turns TLS on By Default on Android P
Related: Android Q Enables TLS 1.3 Support by Default
Related: Google Patches Remote Code Execution Bugs in Android 10
Related: Vulnerability in Network Provisioning Affects Majority of All Android Phones













