GitHub has warned users that they may be targeted in a fairly sophisticated phishing campaign that the company has dubbed “Sawfish.”
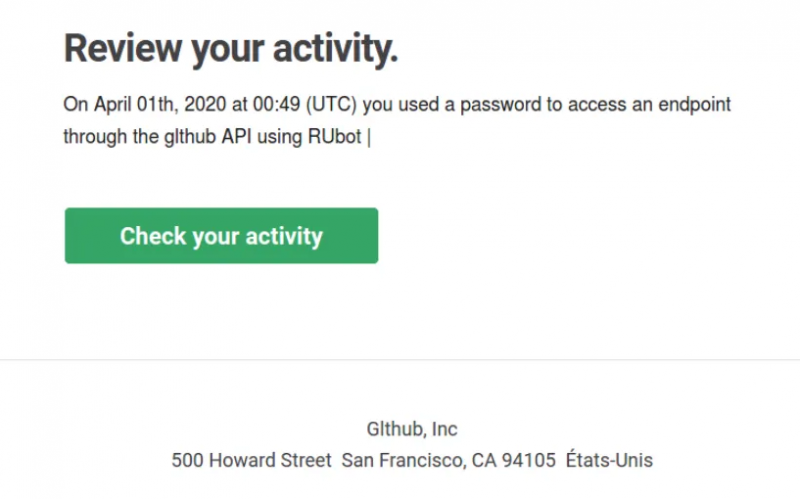
According to the Microsoft-owned company, many of its users have received phishing emails claiming that unauthorized activity has been detected or that a change has been made to their account. The links included in these emails lead to a fake GitHub login page set up to harvest the victim’s username and password and send them to the attackers.
GitHub has pointed out that this phishing campaign has several noteworthy aspects. For example, the phishing page also instructs users who rely on two-factor authentication to protect their account to enter the code generated by their time-based one-time password (TOTP) application. This allows the attackers to hack into accounts protected with this type of system, but the company says users who rely on hardware security keys are not vulnerable.
GitHub also noted that the phishing emails often come from legitimate domains that have been compromised, and the attacks are often aimed at active users working for tech companies in various countries. These users are apparently targeted on the email addresses they used for public commits.
The attackers have also been observed using URL shortening services to hide the final destination of the links included in the phishing emails, and in some cases victims are first directed to a compromised legitimate website before being redirected to the phishing page.
“In many cases, the attacker immediately downloads private repository contents accessible to the compromised user, including those owned by organization accounts and other collaborators,” GitHub said.
Users who believe they have fallen victim to this attack have been advised to immediately reset their password and two-factor recovery codes, review their access tokens, and take additional steps to secure their account.
In addition to hardware security keys or WebAuthn 2FA, users can protect themselves by using password managers, which automatically enter their password only on legitimate domains.
The list of phishing domains identified by GitHub includes git-hub.co, githb.co, glthub.net, glthubs.com and corp-github.com. GitHub has asked users targeted in the Sawfish campaign to provide the company with information about the sender email and the domain hosting the phishing page. The company believes the attackers will likely continue to set up new phishing domains.
GitHub has not shared any information on who may be behind this attack.
Related: Attackers Used Leaked Passwords to Hack GitHub Accounts















