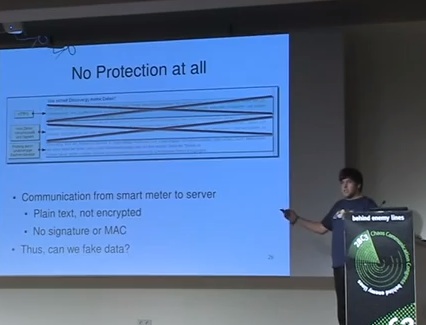
In a talk at the 28th Chaos Communication Congress (28C3) entitled “Smart Hacking For Privacy,” researchers Dario Carluccio and Stephan Brinkhaus described their experiences with smart meters from the German energy provider Discovergy. They said they could guess what’s on your digital TV based on unencrypted signals from the smart meters. They could also spoof the energy usage reported from the meter, a far more serious concern. All of this is because the utility in question misconfigured its SSL.
 According to a blog on NakedSecurity, prior to the talk the Discovergy Web site promised consumers several security features. Among these, that access to consumption data is protected by HTTPS, that the smart meter data relayed back to Discovergy was encrypted and signed with a certificate to prevent forged data, and that this information was independently confirmed. On the day of the talk, however, those claims disappeared.
According to a blog on NakedSecurity, prior to the talk the Discovergy Web site promised consumers several security features. Among these, that access to consumption data is protected by HTTPS, that the smart meter data relayed back to Discovergy was encrypted and signed with a certificate to prevent forged data, and that this information was independently confirmed. On the day of the talk, however, those claims disappeared.
The researchers, in seeking to see whether the security claims were true, quickly discovered that the SSL certificate for the site was badly misconfigured so the data in transit wasn’t actually encrypted. This lead to a more interesting discovery: Discovergy polled their smart meters every two seconds, meaning the utility collected and maintained a fairly accurate and very granular record of home usage. The unencrypted data in transit could potentially allow anyone to collect and maintain a similar record of their own—which is what they did.
Based on these records, the researchers said they could guess what movies people were watching in the home. This is similar to research I wrote about last November from the University of Washington, where the use of switched mode power supplies (SMPS) in digital TVs provided energy fluctuations that could reveal what programs were being watched. Here, too, granular power fluctuations matched certain video content displayed on a digital TV in the test.
The researchers, of course, attempted to do more. They used the smart meter’s MAC address to spoof the unencrypted packets going back to Discovergy, and therefore compromise the record being kept at the utility. Not only could they tamper with the smart meter results, they managed to manipulate data to specific spikes and valleys. In one report, the energy usage fluctuations spelled out “U have been hacked”.
They note that since they used a Windows program (not Linux) to do this manipulation, just about anyone can do this (assuming they release the Windows tool to the masses, which they (so far) have not).
In the 28C3 audience was Discovergy CEO, Nikolaus Starzacher, who came on stage during the Question and Answer period and vowed to address these and other the other issues cited by the researchers.
Fun and games aside, smart meter attacks like this could cost utilities millions in potential theft of service (one could depress actual energy usage) or cost consumers large sums in targeted high bills (one could increase actual energy usage). This is a very serious problem. If the energy provider has not secured the smart meter or the smart meter data in transit, then the Smart Grid is unlikely to result in the efficiency and savings that many have promised.
The complete 28C3 Smart Hacking For Privacy smart meter presentation is embedded below.














