Security researchers have discovered five zero-day vulnerabilities and a further 15 easy misconfigurations in Salesforce Industry Cloud, potentially affecting tens of thousands of organizations.
Salesforce Industry Cloud (aka Salesforce Industries) comprises a collection of industry-specific tools able to easily build custom CRM extension solutions for different industry sectors – such as healthcare, financial services, manufacturing, communications, and government public sector organizations. The process is built on the technology Salesforce acquired with its purchase of Vlocity in June 2020 and the use of OmniStudio low-code tools.
AppOmni is a SaaS security platform. More than 25% of its Salesforce customers use Industry Cloud, and the firm felt it incumbent to explore the security of the product. The subsequent research discovered five zero-day vulnerabilities and a further 15 potentially easy but severe misconfigurations.
The research was reported to Salesforce. It was Salesforce who declared five to be vulnerabilities and rapidly fixed them. Three were fixed at the Salesforce end and require no action by customers; but two need customer involvement. If customers do not follow the instructions sent to them by Salesforce, they will remain actionable vulnerabilities.
The remaining 15 issues are not vulnerabilities, but rather misconfiguration traps that are easy to adopt – and the AppOmni researchers believe many user organizations have misconfigured CRM clouds.
Aaron Costello, Chief of SaaS security research at AppOmni, explains: “My research looks at common misconfigurations and risks that can occur within any of the industry clouds – ways in which customers may misconfigure permissions or access controls that could cause risk. It looks at insecure default settings.”
Salesforce Health Cloud, for example, is designed to improve healthcare operations by streamlining workflows, and enhancing care coordination.
“So, when a customer purchases – let’s say Health Cloud,” he continued, “by default, there are security controls that are not in place. As part of the research, I identified more than 20 risks, and these were provided to the Salesforce security team for review. Salesforce then deemed that five of those risks should be considered vulnerabilities and patched them.”
The basic problem for the remaining 15 issues is difficult to solve. The purpose of Salesforce Industries is to allow organizations to build customized Salesforce CRMs easily, inexpensively, and at speed. It provides a low-code solution that can be built largely by just checking boxes. The builder requires a greater knowledge of the business than of programming – and this is an attractive and valuable combination for business leaders.
The problems come from the mismatch between the potential security knowledge of the box checker and the complexity of the finished Salesforce CRM solution. It is too easy for the customer to check a box and accept the defaults without recognizing the consequences.
“These are non-technical, or not very technical, people with little coding experience using solutions to get things done more easily, but without understanding the risks associated with the features,” explained Costello.
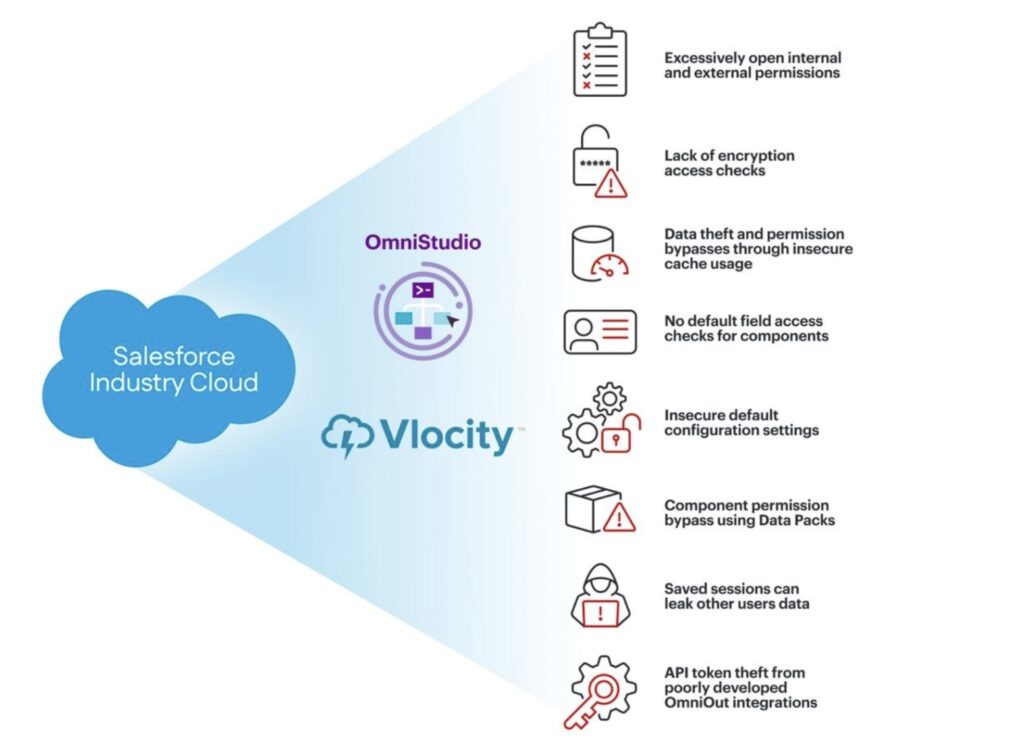
Many of the discovered pitfalls involve access permissions. It’s not always vital – for example if a workflow being developed by this method cannot be accessed, then the default access settings are irrelevant. But if the workflow is accessible by others, or itself accesses other systems, then access controls are essential – and the low-code developer may be unaware of the effect, or lack of effect, of the default settings.
It could be devastating. “These security issues can lead to massive breaches. When we look at the kind of industries that are using one of the Salesforce Industry Clouds, like Health Cloud, for example, the impact could be the disclosure of personal health information for a very large number of people,” explains Costello. The same principle applies to all the Industry Clouds – including financial services, government public sector organizations, communications, manufacturing, consumer goods, education, and automotive dealer networks.
AppOmni developed automated scans for all the potential misconfigurations it had discovered to gauge the extent of the problem. It found widespread risk in all its customers using Salesforce Industry Clouds. By extension, comments Costello, “There are likely tens of thousands of other organizations that are more than likely affected by at least one of these misconfigurations. It’s a very widespread problem.”
Full details of the misconfiguration issues, and how to correct them, are included in the research paper (PDF).
Related: Misconfigured HMIs Expose US Water Systems to Anyone With a Browser
Related: Microsoft Warns of Attackers Exploiting Misconfigured Apache Pinot Installations
Related: Low-Code, High Risk: Millions of Records Exposed via Misconfigured Microsoft Power Pages
Related: Massachusetts Health Insurer Data Breach Impacts 2.8 Million


