More than 400 SAP NetWeaver instances are exposed to attacks targeting a zero-day vulnerability patched last week, the nonprofit cybersecurity organization The Shadowserver Foundation warns.
The exploited issue, tracked as CVE-2025-31324 (CVSS score of 10/10) and described as a missing authorization check, impacts the Visual Composer Metadata Uploader component of NetWeaver, and allows attackers to upload malicious executables.
On April 24, SAP released security note 3594142 that addresses the flaw, and updated its April 2025 Security Patch Day advisory to add the note, urging customers to apply the patch as soon as possible.
Cybersecurity firm ReliaQuest, which uncovered the bug during an investigation into intrusions at multiple customers, observed threat actors exploiting CVE-2025-31324 to deploy JSP webshells in a root directory and then leveraging them for payload deployment, code execution, and lateral movement.
Shortly after the security defect was publicly disclosed, application security firm Onapsis told SecurityWeek it was seeing over 10,000 internet-facing SAP applications, but noted that the vulnerable Metadata Uploader component was not enabled by default, and that not all instances were impacted.
“The exploitation grants the attackers full control over SAP’s critical business processes and information, which could result in espionage, sabotage, and fraud,” Onapsis said.
Over the weekend, The Shadowserver Foundation warned that it was seeing over 450 SAP NetWeaver instances vulnerable to CVE-2025-31324.
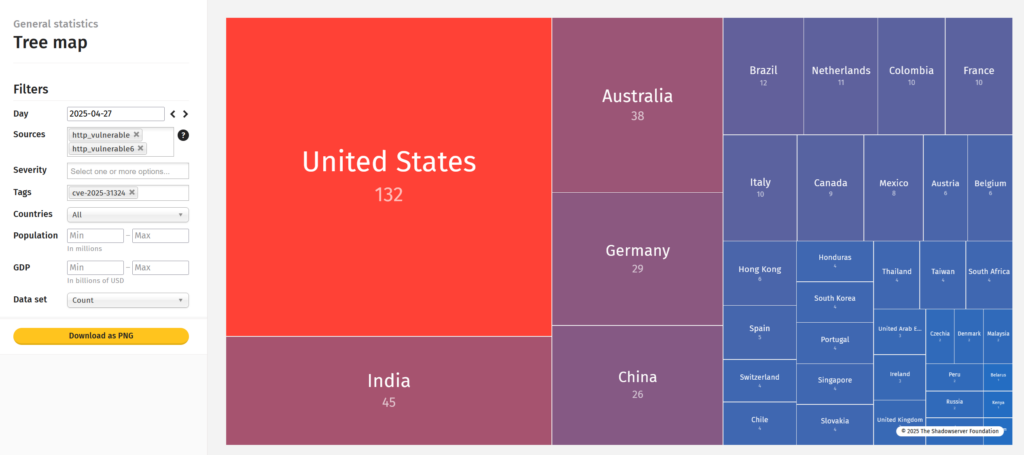
As of April 28, 427 instances are still vulnerable, data from The Shadowserver Foundation shows. Most of these are in the US (132), followed by India (45), Australia (38), Germany (29), and China (26).
Considering the vulnerability’s ongoing exploitation and the critical role SAP applications have within business environments, organizations are advised to apply the patches for CVE-2025-31324 as soon as possible.
Related: SAP Zero-Day Possibly Exploited by Initial Access Broker
Related: SAP Patches High-Severity Vulnerabilities in Commerce, NetWeaver
Related: Organizations Warned of Exploited SAP, Gpac and D-Link Vulnerabilities
Related: SAP AI Core Vulnerabilities Allowed Service Takeover, Customer Data Access


