A new zero-day vulnerability in Windows was made public on Twitter by the same researcher who published an exploit for a bug in the Windows Task Scheduler at the end of August.
The newly revealed security flaw impacts the Microsoft Data Sharing library dssvc.dll, and can be exploited by attackers who already have access to the affected system.
The researcher who found the bug, and who goes by the online handle of SandboxEscaper, also published a proof-of-concept (PoC) on GitHub. The code deletes files from the system that only admins would normally have the permission to delete and causes the system to crash.
“Not the same bug I posted a while back, this doesn’t write garbage to files but actually deletes them.. meaning you can delete application dll’s and hope they go look for them in user write-able locations. Or delete stuff used by system services c:windowstemp and hijack them,” SandboxEscaper says.
The vulnerability impacts only the latest Windows versions, as the Data Sharing Service was introduced in Windows 10 (Windows Server 2016 and Server 2019 are also affected). Cyber-security expert Kevin Beaumont explains that the exploit abuses “a new Windows service not checking permissions again.”
“This is an elevation of privilege zero-day vulnerability in Microsoft’s Data Sharing Service (dssvc.dll), which is used to broker data between applications,” Tom Parsons, Head of Research at Tenable, told SecurityWeek in an emailed comment.
Given that Windows 10 is the second most prevalent Microsoft operating system after Windows 7, the vulnerability could prove attractive to attackers, he suggests.
“To put the threat into perspective, an attacker would already need access to the system or combine it with a remote exploit to leverage the vulnerability. This could be exploited to facilitate lateral movement within an organization or even potentially destructive purposes – such as deletion of key system files rendering a system inoperable,” Parsons says.
Exploitation of this vulnerability, however, isn’t that easy, as even SandboxEscaper said it right from the start. As Beaumont points out, the bug might be “fairly difficult to exploit in a meaningful way.” The most likely scenario would involve targeting OEM drivers, but it’s not practical, he says.
Mitja Kolsek, CEO of ACROS Security and co-founder of 0patch, was among the first to confirm that the published PoC works. Within hours, however, the 0patch team came up with a micropatch for the bug. A micropatch for Windows Server 2016 was also announced.
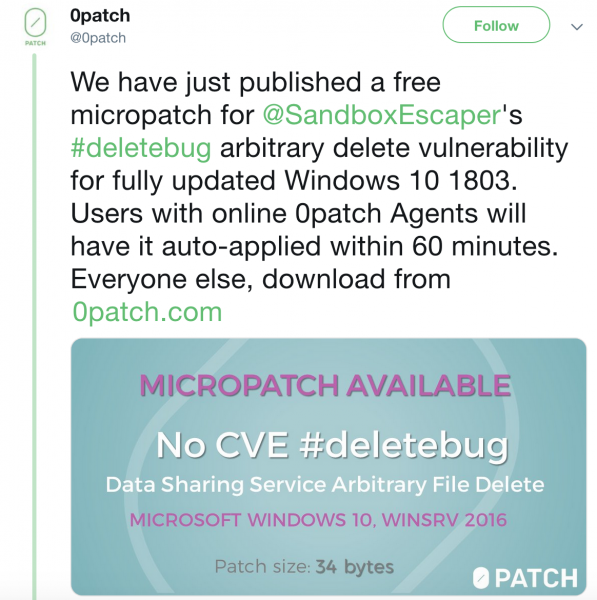
It’s not surprising that 0patch released a fix so fast, as the community is focused on delivering small patches for bugs that vendors haven’t had time to address yet.
At the end of August, they released a micropatch for the Windows Task Scheduler zero-day found by SandboxEscaper. More recently, they released a fix for a Microsoft JET Database Engine flaw that Trend Micro’s Zero Day Initiative (ZDI) made public in late September. In fact, they addressed the issue twice, as Microsoft’s official patch was incomplete.
Related: Exploit Published for Windows Task Scheduler Zero-Day
Related: ZDI Shares Details of Microsoft JET Database Zero-Day














