More Than 2 Petabytes of Unprotected Medical Data Found on Picture Archiving and Communication System (PACS) Servers
The results of 13 million medical examinations relating to around 3.5 million U.S. patients are unprotected and available to anyone on the internet, SecurityWeek has learned. This is despite the third week of this year’s National Cybersecurity Awareness Month (week beginning 19 October 2020) majoring on ‘Securing Internet-Connected Devices in Healthcare’.
The details were disclosed to SecurityWeek by Dirk Schrader, global vice president at New Net Technologies (NNT — a security and compliance software firm headquartered in Naples, Florida). He demonstrated that the records can be accessed via an app that can be downloaded from the internet by anyone. The records found are in files that are still actively updated, and provide three separate threats: personal identity theft (including the more valuable medical identity theft), personal extortion, and healthcare company breaches.
Schrader examined a range of radiology systems that include an image archive system — PACS, or picture archiving and communication system. These contain not only imagery but metadata about individual patients. The metadata includes the name, data of birth, date and reason for the medical examination, and more. Within a hospital, the imaging systems (X-rays, MRIs etc) are also stored in the PACS. The treating physician needs ready access to the images to confirm the current treatment. Schrader simply used Shodan to locate systems using the DICOM medical protocol. Individual unprotected PACS systems within the return of 3,000 servers were located manually. One, for example, contained the results of over 800,000 medical examinations, probably relating to about 250,000 different patients.
Although unprotected servers were found manually by Schrader, he chose this route to demonstrate that no hacking skills are required in this process. An attacker could have written a script to separate the protected from the unprotected servers in a fraction of the time. In total, he had access to more than 2 petabytes of medical data.
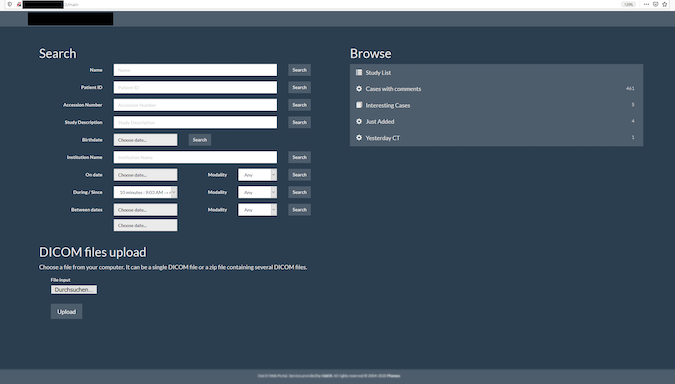
He found three ways to access the stored data. The first is what the physician would do, via a configurable freeware DICOM Viewer app downloaded from the internet and configured by the user. Viewers can be found simply by searching for ‘DICOM viewer’. Schrader specifically used the Radiant DICOM Viewer. An even simpler method is directly via the web browser. The server is located via Shodan, and because it is unprotected, an attacker can often both download and upload to that server, and manipulate the content. “I can upload false data,” Shrader told SecurityWeek, “without hacking.” The third method is that some of the servers offer a full download of the entire dataset directly through the browser.
The level of detail on individuals includes names and sometimes social security numbers — potentially allowing identity theft. The type and result of the medical examination is also included, allowing an attacker to collect details on patients who have proved COVID or HIV positive, or had a mastectomy procedure — potentially allowing personal extortion. In some cases, active folders can be accessed — and updated — by an attacker simply through a browser. If these folders are updated with a weaponized PDF or JPG, then the attacker has a potential route to deliver malware and ultimately ransomware to the healthcare institution concerned. Where a physician is using the content of the PACS server to check on a patient’s current treatment, and downloads a weaponized file, he or she could potential open route for malware to infect the institution, ultimately leading to a major ransomware attack.
Schrader has been investigating this issue for several years, looking at healthcare institutions around the world. In December 2019, he sent disclosure notices to the administrators of 120 unprotected systems in the U.S. Sixty-nine administrators completely ignored the warnings, including 19 children’s hospitals. Elsewhere, responses have been better. In general, the response from Europe and the UK has been positive, and the data has been secured. The U.S., India and Brazil are the primary culprits today, but other unprotected PACS systems exist in Australia and Canada – and one in France. The figures he gave to SecurityWeek relate entirely to the U.S.; and rather than exposed systems being removed, new systems are still being added without adequate or any authentication requirements.
Having obtained the IP addresses from Shodan, Schrader went on to run vulnerability checks against the U.S. institutions, and found, he told SecurityWeek, “around 600 high severity vulnerabilities in around 170 U.S. systems connected to the internet;” suggesting that the systems are not just unprotected, but also unmanaged. “There are numerous end-of-life vulnerabilities, and several Microsoft vulnerabilities at the highest risk level. There is no reason for a picture archiving system to remain unpatched — it’s like these systems have been connected to the internet and just forgotten.”
Schrader has found no hard evidence that PACS content has been abused by criminals, “But my suspicion,” he told SecurityWeek, “is that criminals are already using this method because it is so easy.” The solution to the problem is simple — PACS servers should require adequate access authentication, or be removed from the internet. In the meantime, many millions of sensitive medical records can be accessed by anyone at any time.
Related: German Hospital Hacked, Patient Taken to Another City Dies
Related: As Healthcare Industry Transforms Overnight, Tech Community Must Act
Related: Attack Surface Growing for Healthcare Industry
Related: Governments Asked to Stop Cyberattacks on Healthcare Systems














