Enterprise users have been warned that cybercriminals may be trying to phish their credentials by luring them with fake emails that appear to be related to services offered by security company Zix.
Zix provides cybersecurity, compliance and productivity solutions to 21,000 organizations, and cybercriminals have been leveraging the company’s reputation in a phishing campaign aimed at enterprises.
Email security company Armorblox said on Tuesday that it has observed an attack on customer environments across Microsoft Exchange, Office 365 and Google Workspace.
“Although the potential account exposure of this attack campaign was close to 75,000 mailboxes, our threat research team found that a select group of employees – usually across departments – were targeted within each customer environment,” Armorblox explained in a blog post.
In the case of one organization, the emails targeted the CFO, the director of marketing, the director of operations, and a professor. In another company, the attacks targeted the president and the SVP of finance and operations.
“While the spread is seemingly randomized, attackers might also have deliberately chosen their victims to be across departments and to contain a good mix of senior leadership and individual contributors. These employees are unlikely to communicate often with each other when they receive an email that looks suspicious,” Armorblox said.
The fake emails are titled “Secure Zix message” and they instruct recipients to click on a button within the email to read the “secure message.” Once the button has been clicked, the victim is taken to a phishing page.
The fake emails do not appear to be exact copies of legitimate Zix notifications, but they do borrow some design elements, enough to potentially trick some unsuspecting users.
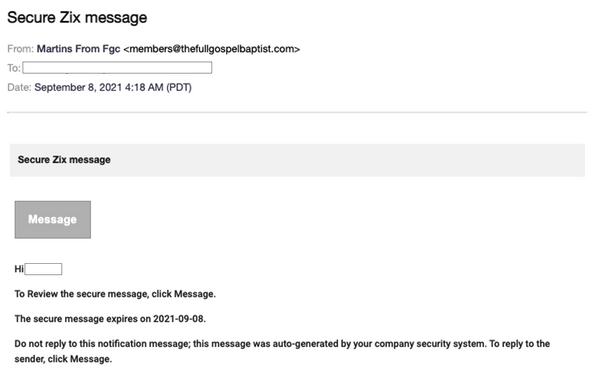
In addition to abusing Zix’s name, the campaign leverages what appears to be a domain belonging to a religious organization in the United States. Armorblox noted that the malicious emails passed authentication mechanisms such as DMARC.
Armorblox said it was unable to obtain the final payload delivered in this campaign, but the company believes it was most likely a phishing page for Zix or other credentials. In many similar campaigns observed by Armorblox, the attackers — impersonating various brands in the emails they sent out — were attempting to lure victims to fake Office 365 login portals.
Zix-themed phishing messages have been making the rounds for months. In May, Zix informed customers about a campaign that leveraged the compromised Microsoft 365 account of a US-based company. The compromised account had been used to send out thousands of fake Zix emails, and a “small subset” of those emails reached Zix customers.
Related: Microsoft: Ongoing, Expanding Campaign Bypassing Phishing Protections
Related: Coinbase Users Face Ongoing Phishing Attacks
Related: Chipotle’s Email Marketing Account Hacked to Spread Malware

