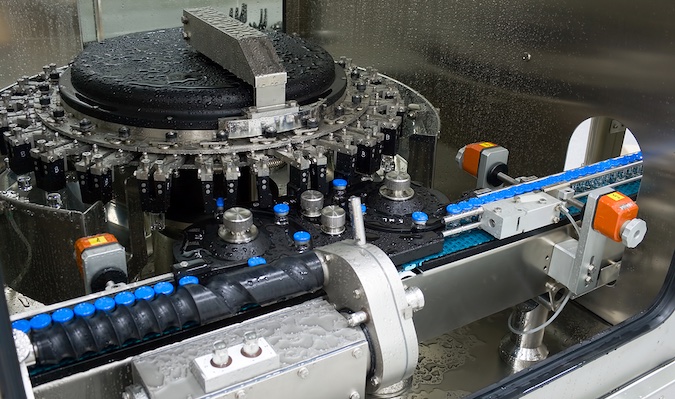
The increased use of automated control systems to manage drug formulations and product quality (particularly for combination drugs) is creating new security risks for the pharmaceutical industry.
Examples of this new vulnerability surfaced in June 2017 when the pharmaceutical sector, along with healthcare and many other industries, were targeted by the Wannacry ransomware. Many organizations were forced to halt operations and drug production. When we look back at what’s already happened, it becomes clear that going forward risks will likely increase as more pharmaceutical operations adopt IoT technology.
According to Grandview research, the global IoT in healthcare market size is projected to reach USD 534.3 billion by 2025 expanding at a CAGR 19.9% over the forecast period. Many analysts also cite the pharmaceutical sector as one of the top five industries for adopting this technology.
While pharmaceutical operations networks were once siloed, today their connection to IT and anywhere access has created an environment that threatens the integrity of drug formulation control systems. What’s more, the elimination of “air-gapping” enables bad actors to penetrate a pharma-based OT environment from either the IT or the operational technology (OT) network.
Unlike other OT networks, pharma-based networks are not just mission-critical, they are life-critical. Because of this, it’s difficult to stop operations to perform routine maintenance or even apply patches when a vulnerability is discovered. Furthermore, in remote drug trial facilities, it is difficult to maintain an up-to-date inventory capable of zeroing in on specific devices to perform the servicing needed to keep operations running smoothly and securely. The result is that vulnerability windows can remain open indefinitely and be susceptible to both known and unknown threats.
While pharmaceutical facilities are protected by perimeter security, once inside third-parties (e.g. partners, contractors, consultants, etc.) can gain easy access to restricted areas. This is especially true in remote locations that may not maintain the samelevel of security as the main campus.
From a compliance standpoint, few verticals have more exacting standards than pharmaceutical manufacturing. One small deviation in a drug formulation can mean the difference between life and death. Furthermore, few industries are subject to as many regulations as the pharmaceutical sector.
As a result, protecting pharmaceutical OT networks from external attacks, insider threats and human error requires deep awareness of the state, configurations and changes made to every device. This includes the ability to continuously monitor and compare the specific condition of devices with current vulnerability data to remediate threats and avoid false positives.
If unintended changes occur, they must be captured and logged in real-time, as well as historically. This should include the user that logged in, what processes were running, the code downloads initiated, as well as all changes in the environment. Capturing and maintaining this detailed audit trail not only accelerates incident response, it also enables pharmaceutical manufacturers to document and demonstrate compliance with organizational security policies.
Learn More About OT Security at SecurityWeek’s ICS Cyber Security Conference

