DHS Publishes Enhanced Analysis Report on GRIZZLY STEPPE Activity
The Department of Homeland Security (DHS) National Cybersecurity and Communications Integration Center (NCCIC) on Friday published a new report providing additional indicators of compromise (IOC) and analysis using the cyber kill chain to detect and mitigate threats from the Russia-linked “GRIZZLY STEPPE” hackers.
On Dec. 29, 2016, the DHS and FBI published an initial Joint Analysis Report (JAR) detailing the tools and infrastructure used by Russian hackers designated by DHS as “GRIZZLY STEPPE” in attacks against the United States election. The previous report, however, didn’t deliver on its promise, security experts argued.
While the original report included a series of IOCs, some said that they were of low quality, had limited utility to defenders, and were published as a political tool attempting to connect the attacks to Russia.
The new report is described by DHS as an Analytical Report (AR) providing a “thorough analysis of the methods threat actors use to infiltrate systems” in relation to the GRIZZLY STEPPE hackers. The report provides additional details on IOCs, along with analysis along phases of the cyber kill chain, and suggests specific mitigation techniques that could be used to counter GRIZZLY STEPPE attackers.
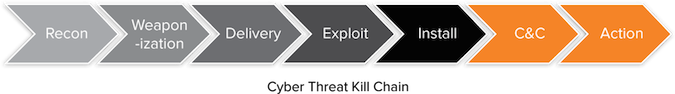
Utilizing the Cyber Kill Chain to Analyze GRIZZLY STEPPE
DHS analysts leveraged the Cyber Kill Chain framework created by Lockheed Martin that describes the phases of an attack. The report summarizes the activity of the campaign using each phase of the Cyber Kill Chain, which are Reconnaissance, Weaponization, Delivery, Exploitation, Installation, Command and Control, and Actions on the Objective.
The report also provides detailed host and network signatures to help defenders detect and mitigate GRIZZLY STEPPE related activity, including additional YARA rules and IOCs associated with the attacks.
The DHS has previously said that two different actors participated in the political attacks, one in the summer of 2015, namely APT29, and the other in spring 2016, namely APT28. The former is also known as Cozy Bear, or CozyDuke, while the latter is referred to as Fancy Bear, Pawn Storm, Strontium, Sofacy, Sednit and Tsar Team.
DHS recommends that security teams read multiple bodies of work from various sources concerning GRIZZLY STEPPE.
“While DHS does not endorse any particular company or their findings, we believe the breadth of literature created by multiple sources enhances the overall understanding of the threat. DHS encourages analysts to review these resources to determine the level of threat posed to their local network environments,” the agency said.












