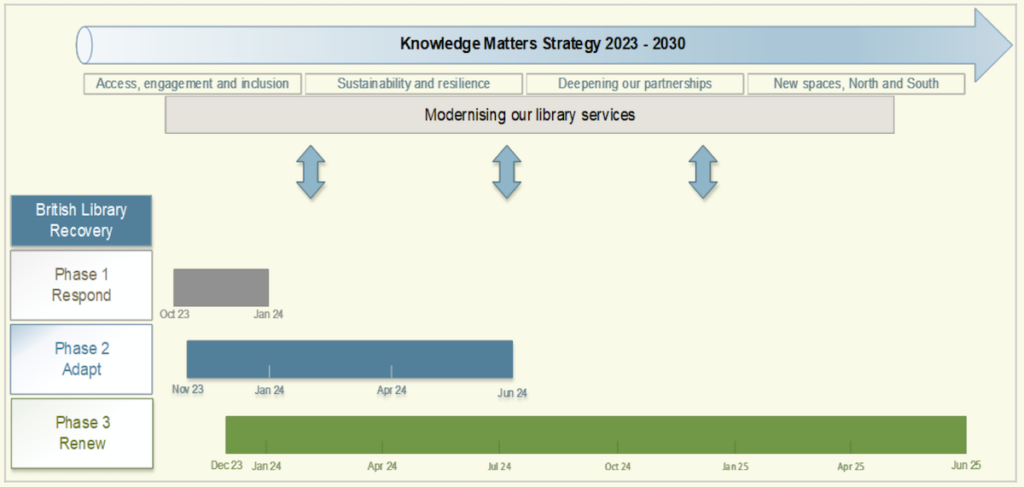
The British Library has shared details on the destructive ransomware attack it experienced in October 2023. Although the attack on the national library of the UK occurred five months ago, the Library’s infrastructure won’t be rebuilt until mid-April 2024, and then the full restoration of systems and data can begin.
The attack
The attack was destructive. Apart from exfiltrating around 600 Gb of data, the attackers deleted logs, encrypted systems, destroyed servers, and locked out all users.
Rhysida claimed responsibility and published data to prove its involvement. Rhysida is relatively new – active since May 2023. It was the subject of a joint FBI/CISA advisory on November 15, 2023. The advisory notes discovered similarities between Rhysida and Vice Society. This includes similar TTPs, and inactivity on the Vice Society’s leak site from shortly after the appearance of Rhysida.
By January 2024, Rhysida had claimed more than 70 victims. More recently it was involved in the MarineMax attack. It is believed to operate as a RaaS organization.
After exfiltrating data, the attackers encrypted information and systems and destroyed some servers to inhibit recovery and cover their tracks. The damage to servers has been the most impactful aspect of the attack – recovery from backups has been hampered by a lack of infrastructure for recovery. Major software cannot be brought back in its original form either because it is no longer supported by the vendor, or it simply won’t run on the new hardware.
The burnt earth approach from the attackers against the British Library means it is unlikely the point of entry and means of access will ever be definitively proven. However, the first detected unauthorized access was found on a Terminal Services server. This had been installed to cope with the hugely expanded remote access requirements caused by the Covid pandemic.
The Library suspects that access was gained here through “the compromise of privileged account credentials, possibly via a phishing or spear-phishing attack or a brute force attack.” MFA was in use across the network, but notably not on this server — its implementation had been delayed for reasons of practicality and cost. “It is considered likely that the absence of MFA contributed to the attackers’ ability to enter the system [although] the exact point and method of entry cannot be stated with certainty,” says the report.
If the Library’s assumed timescale is accurate, the damage was done in three days. “Forensic investigation and analysis of records indicates the strong likelihood that the criminal actors initially gained access at least three days before the incident became apparent,” says the report.
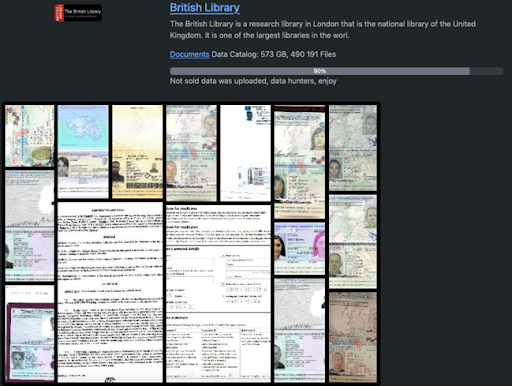
The Library neither paid the demanded ransom nor contacted the attackers. As a publicly funded organization, it had no scope for maneuver against the UK government policy disseminated by the NCSC: never pay. With no payment, the stolen data (which included personal data of users and staff) was put up for auction by the attackers and later dumped on the dark web. According to Rhysida, the exfiltrated data amounted to 573 Gb and 490,191 files. The group sold 10%, and dumped the remaining 90% with the message, ‘data hunters enjoy’.
The lessons
Use MFA. The most likely access point for Rhysida was a new server with no MFA implementation. “It is considered likely that the absence of MFA contributed to the attackers’ ability to enter the system,” says the report. The Library intends to ‘substantially improve’ both its MFA and PAM implementations.
Be wary of the threat from legacy systems. The threat from legacy systems is that you cannot always patch them to prevent an attack, nor can you recover them after an attack. The result can be greater cost and time to rebuild from new.
Implement network segmentation. This had not been possible on the Library’s legacy network topology but will be included after the ‘rebuild and renew’ program. The lack of segmentation, says the report, “meant that the attack was able to cause more damage than would have been possible in a modern network design.”
Use the cloud. “Our core email, finance, HR and payroll systems are cloud-based and are functioning normally, having been largely unaffected by the attack,” notes the report. The new infrastructure will have a hybrid compute landscape that leverages the benefits of cloud for development, application, and virtualization. It doesn’t eliminate risk but changes it into something more manageable.
Understand the value and benefit of secure backups. The Library’s new backup system will comprise “a robust and resilient backup service, providing immutable and air-gapped copies, offsite copies, and hot copies of data with multiple restoration points on a 4/3/2/1 model.”
Be financially prepared. As a publicly funded organization under the aegis of (that is, funded by and accountable to) the UK government’s Department for Culture, Media, and Sport (DCMS), the Library could have, in extremis, called for additional restorative funds. Private companies have no similar safety net, but the Library did not require such aid. It had already set aside funds for future infrastructure spending (its Knowledge Matters Strategy) and was able to bring forward this planned expenditure.
Access to these funds were happenstance for the British Library, but ensuring access to emergency funds is an important part of future planning.
The report makes no mention of cyberinsurance, either past, present, or intended. It may be that the DCMS is effectively the insurance provider, or it may be a condition of insurance that its use is not disclosed. For most private companies, however, cyberinsurance should be considered as potentially relevant to future financial and risk planning.
Have the right salary scales. The report notes that its ‘rebuild and renew’ program will be difficult “without reconsideration of how the Library remunerates high-demand IT skills.” There is some acceptance that the capacity and capability within the Technology department was already overstretched prior to the attack.
Grasp and maximize the silver lining. “The substantial disruption of the attack creates an opportunity to implement a significant number of changes to policy, processes, and technology that will address structural issues in ways that would previously have been too disruptive to countenance,” says the report.
Related: Cyber Insights 2024: Ransomware
Related: EquiLend Ransomware Attack Leads to Data Breach
Related: Recent TeamCity Vulnerability Exploited in Ransomware Attacks
Related: Critical Infrastructure Organizations Warned of Phobos Ransomware Attacks


