Bitdefender on Monday announced the availability of a free tool that organizations can use to recover files encrypted by DarkSide, a piece of ransomware that cybercriminals claim helped them make millions.
DarkSide is a ransomware-as-a-service (RaaS) offering that was first announced on cybercrime forums in August 2020. DarkSide operators have been making money not only by encrypting important files on compromised systems, but also by stealing valuable information to pressure victims into paying up.
DarkSide victims have been instructed to pay hundreds of thousands and even millions of dollars to recover their files and prevent data leaks, and the group behind the ransomware said it only targeted companies that could afford to pay up, but claimed that it would not target hospitals, educational institutions, government organizations or NGOs.
The DarkSide ransomware has made headlines for being introduced through a press release, for its affiliate program, for donating some of their profit to charity, and providing customers storage systems for stolen data.
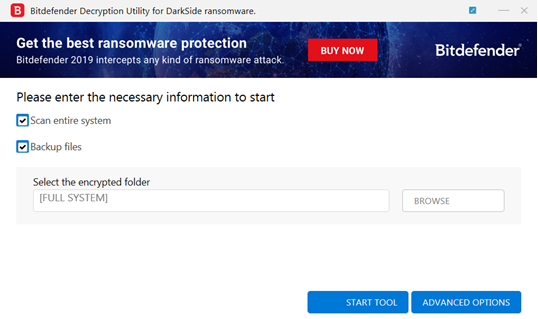
While at this point many DarkSide victims likely restored encrypted files from backups or recovered them by paying the ransom, some companies may be happy to hear that Bitdefender has released a free tool that automatically scans the system for encrypted files and decrypts them.
The tool has to be executed locally on systems where the encrypted files are stored. Users are advised to create backups — a feature that is also available in Bitdefender’s free tool — before initiating the decryption process.
“To remove the encrypted files left behind, you should search for files matching the extension and mass-remove them. We do not encourage you to do this until you made sure that your files can be opened safely and there is no damage to the decrypted files,” Bitdefender said in a blog post announcing the tool.
Related: Free Tool Enables Recovery of Files Encrypted by ThiefQuest Mac Malware
Related: Decryptor Released for Latest GandCrab Ransomware Variants















