A cyber-espionage group has targeted hundreds of industrial companies in South Korea and other countries using malware designed to help hackers steal passwords and documents, industrial cybersecurity firm CyberX revealed on Tuesday.
The campaign, which CyberX has dubbed Gangnam Industrial Style, is ongoing and the company’s threat intelligence team continues to investigate the attacks.
However, CyberX told SecurityWeek that it has not determined where the attacks are coming from or the language spoken by the attackers — attribution is often difficult, but in some cases researchers find clues that reveal the language apparently spoken by the hackers.
In the case of Gangnam Industrial Style, attribution is also made difficult by the fact that the attackers have been using free hosting services for their command and control (C&C) servers.
“We can’t use the usual methods of identifying attackers based on DNS registrations,” explained David Atch, VP of research at CyberX.
Atch also told SecurityWeek that they have not been able to determine the attackers’ motivation. The threat group has been stealing credentials and documents from compromised systems, which based on previously observed, unrelated attacks can allow the hackers to steal trade secrets and intellectual property, perform reconnaissance, and launch ransomware attacks targeting the vicitm’s industrial networks.
According to CyberX, the attackers have been using a new version of an info-stealer known as Separ, which was first spotted in 2017, with links being found to other similar threats that have been around since 2013.
Earlier versions of the malware were only designed to steal passwords, but the one used in the Gangnam Industrial Style campaign also allows hackers to steal files from compromised machines and it uses the Autorun feature for persistence.
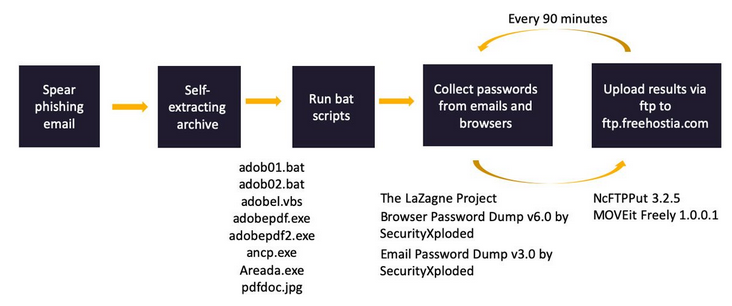
The malware has been delivered via spear phishing emails with various themes, including a request for quotation (RFQ) apparently coming from a Siemens subsidiary for designing a power plant in the Czech Republic, an RFQ apparently coming from a major Japanese conglomerate for the design of a power plant in Indonesia, and an email that appeared to come from a major European engineering company.
CyberX says it has identified over 200 systems that have been hacked as part of this campaign, including ones belonging to a multi-billion dollar South Korean conglomerate that manufactures critical infrastructure equipment, an engineering firm, a chemical plant construction company, and organizations specializing in the manufacturing of steel, pipes and valves.
The malware is delivered inside a ZIP archive file and it appears to be a harmless PDF document. When executed, it maps all network adapters, disables the Windows firewall, harvests browser and email passwords, collects files with extensions that may be of interest to the attackers, and uploads the information to an FTP server.
While over 57% of the targeted companies were located in South Korea, the attackers have also launched attacks against firms in China, Thailand, Japan, Indonesia, Turkey, Germany, Ecuador and the UK. Over half of the targets were in the manufacturing industry, followed by organizations in the steel, engineering, and conglomerate sectors.
Related: South Korea Warns of Flash Zero-Day Exploited by North Korea
Related: South Korea Probes Cyber Shutdown During Olympics Ceremony















