Innocent-looking help files have been used by cybercrooks to distribute a variant of the notorious file-encrypting ransomware CryptoWall, Bitdefender reported.
The security firm spotted a spam run on February 18, when malicious actors sent out bogus “Incoming Fax Report” emails to a couple hundred users. The messages carried a help file with the .chm (compiled HTML) extension.
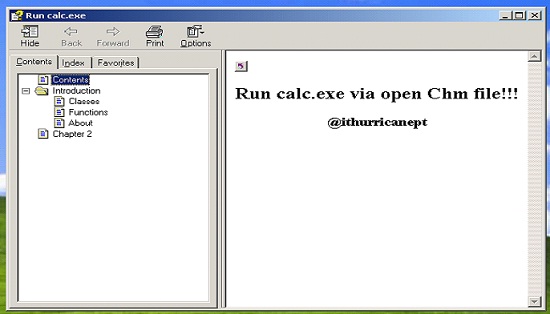
When users opened the file, they were presented with a help window. In the background, a piece of malicious code downloaded the CryptoWall ransomware from a remote server and executed it.
CryptoWall is a well-known piece of ransomware that encrypts important files and keeps them that way until the victim pays a specified amount of money for the decryption key. The latest version of the malware, CryptoWall 3.0, is interesting because it relies on I2P (Invisible Internet Project), an anonymity network also used by Silk Road Reloaded, for command and control (C&C) communications.
Bitdefender, which detects the threat as Trojan.GenericKD.217093, provides an app that can be used to protect computers against CryptoWall by blocking file encryption attempts.
CHM files might seem harmless, but they can run JavaScript code, which makes them effective for cybercriminal operations.
“These CHM files are highly interactive and run a series of technologies including JavaScript, which can redirect a user toward an external URL after simply opening the CHM,” Bitdefender said. “Attackers began exploiting CHM files to automatically run malicious payloads once the file is accessed. And it makes perfect sense: the less user interaction, the greater the chances of infection.”
Because the fake fax emails were designed to look like they were coming from a device in the recipient’s domain, researchers believe the operation was aimed at corporate users.
According to Bitdefender, the attackers used servers located in Vietnam, India, the US, Australia, Spain and Romania to send out the spam emails. The malicious messages landed in the inboxes of users from across the world, including in the United States, Europe and Australia.
Security researcher Yonathan Klijnsma also analyzed this particular campaign back in February. The expert pointed out that the attackers leveraged a proof-of-concept created in November 2014 by a Chinese security engineer who uses the online moniker “ithurricanept.” The PoC demonstrates that CHM files can be used to execute payloads without being detected by antiviruses.
“He simply demonstrated that no A/V would detect this execution in any way. It seems the CryptoWall guys found this out, tested it again and found it still worked fine against A/V’s. They took his POC (literally, they left in the message from the original author) and added some code to download their CryptoWall payload,” Klijnsma told SecurityWeek.
*Updated with additional information from Yonathan Klijnsma
















