Operational resilience is a priority and organizations are decisive about protecting cyber-physical systems (CPS) in today’s consolidated and converged reality
Over the last few years, the pandemic, rapid growth in several sectors and geographies, and the work from home paradigm shift have significantly accelerated the convergence of IT and operational technology (OT) networks and necessitated a consolidated strategy to address cyber risks across cyber-physical systems (CPS). Companies began to rise to the challenge and streamlined their IT and cybersecurity strategies to reflect this reality. This meant:
• Bringing OT and IT experts together to define a consolidated strategy
• Looking for efficiency and cost optimizations across the cybersecurity product stack that can address both fields
• Mapping their progress against an industry-defined and tested framework, to understand where they stand versus the competition and communicate risk and opportunities to the board
Cybersecurity, especially for CPS, evolved from being a cost factor, to an enabler for digital transformation, to a differentiating advantage for companies that truly excel at it.
Today, our physical world is very dependent on its digital components as we strive for greater efficiency, automation, and cost and time savings by leveraging the power of AI and insights from data analytics. These advancements all require CPS interconnectivity so we can share data and take advantage of simplified and more efficient workflows.
As a result, every company is on a journey to better and more efficient protection of CPS. The most successful companies do a great job of understanding where they are on the journey and how to structure their next steps. One framework I find especially useful towards this goal is the Gartner OT/CPS Security Journey.
In my discussions with CISOs and security leaders, the framework is very helpful in:
• Benchmarking against peers, competitors, and the industry as a whole
• Highlighting the risk to the organization relative to the market, which is important in communicating risk to the board
• Explaining the need for investment in CPS security and the priorities
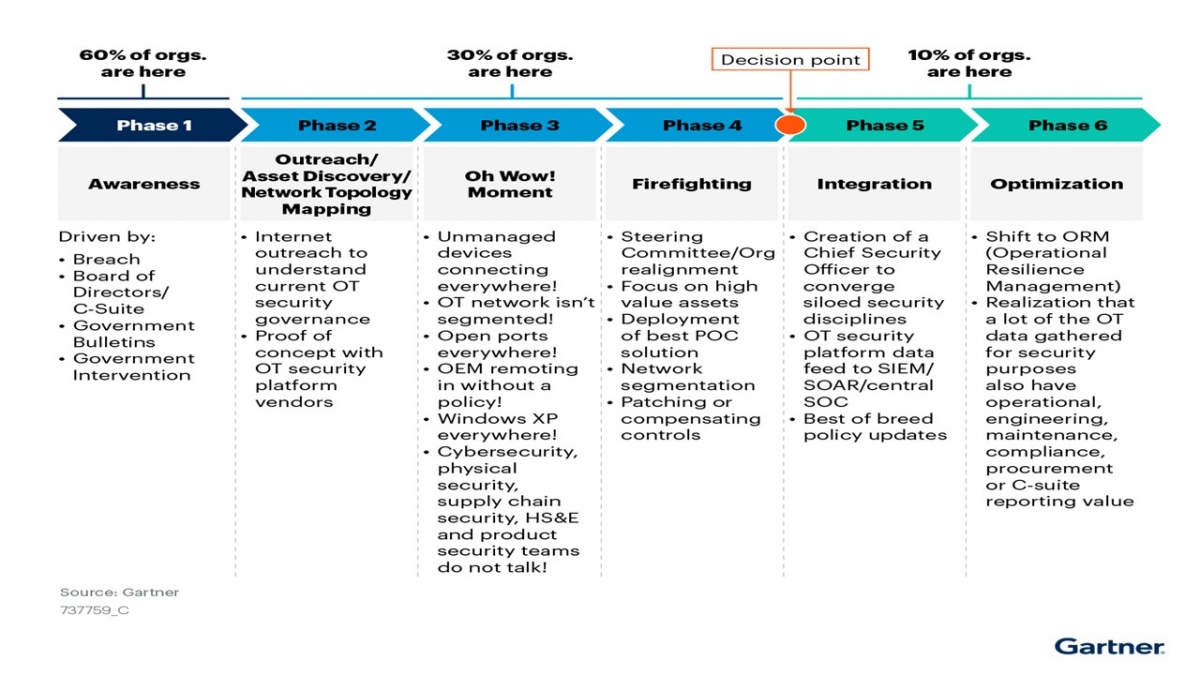
The Gartner OT/CPS Security Journey has six phases. Below are some of my key learnings, recommendations, and best practices to help you benchmark with your peers and further your journey.
1. Awareness. Whether prompted by a breach, the pandemic, or geopolitical conflict, organizations are being forced to re-prioritize a combined IT/OT security strategy, which usually reveals challenges in IT and OT teams working together. It’s the “storming” stage all teams must go through as they understand more deeply the unique CPS cybersecurity requirements and bring together the necessary expertise.
2. Outreach / Asset Discovery / Network Topology Mapping. Before applying any security measures, the teams need to understand what they have, how it’s connected, and the security posture of those devices. In this stage the teams learn more about their current vendor capabilities and start to form a strategy to define consolidated governance across IT and OT networks. Collaboration between the teams typically improves as they are working on concrete challenges together and seeing progress.
3. The “Oh Wow!” Moment. The name for this phase is spot on. Expect the unexpected in an environment that has been largely unseen, unmanaged, and increasingly interconnected in the last couple of decades. Suddenly, teams are discovering unmanaged assets everywhere, connectivity that shouldn’t be there, and many vulnerabilities across devices—most of which are unpatchable. Many security challenges are unearthed, but at least teams have visibility into those now.
4. Firefighting. With so much to do based on the findings of the previous stage, it’s easy to be overwhelmed. This stage is a tipping point where the best organizations go through a process to prioritize efforts, not just throw resources at the findings. Having a clear definition of business objectives is imperative, as this phase is not only about closing security risks, but also about taking advantage of the advances in technology and connectivity so that CPS interconnectivity serves the larger digitalization and cost optimization priorities of the company. This is where great companies excel in showing how cybersecurity can be a competitive advantage.
5. Integration. This phase requires the most work, as implementation takes time and thoughtful allocation of resources. Leveraging platforms that lean into integration helps greatly reduce implementation effort and cost. At this point the organization is also aligned, centralizing responsibility and accountability for securing the OT network with the CSO or CISO for consolidated governance and continuity of monitoring and reporting. This holistic process across IT and OT is the foundation upon which teams can build optimizations.
6. Optimization. Beyond reducing risk and increasing operational efficiency, this is the stage in which organizations start to realize the power of the data and analytics they can gather from the integrated environment. Teams have an opportunity to discover even more ways in which to improve the business. Although it’s hard to get here, I’ve personally seen a number of organizations reach this point and it’s very fulfilling to be able to demonstrate all the ways in which digitalization and CPS convergence can help drive business outcomes.
The last two years have underscored that OT networks are critical to operations, and therefore extremely valuable. Revenue is generated and customers’ lives are improved when OT networks are up and running. However, a surge in attacks on these systems have demonstrated how vulnerable they are. Fortunately, operational resilience is now a priority and organizations are decisive about taking the right next steps to protect these systems more effectively in today’s consolidated and converged reality.
Read: OT Data Stolen by Ransomware Gangs Can Facilitate Cyber-Physical Attacks

