The U.S. Air Force has awarded CSC with a contract to provide cybersecurity services for the 33rd Network Warfare Squadron (NWS) based at Lackland Air Force Base in San Antonio, Texas. The contract, which has a one-year base period and two option years, has an estimated total three-year value of $30 million.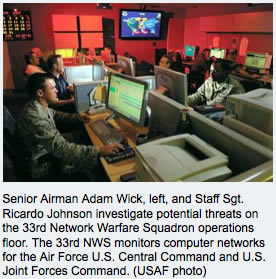
As part of the contract, CSC will isolate, contain and prevent intrusive activities on the Air Force automated information systems and networks. CSC will also plan, coordinate, analyze and report on the results of managed network intrusion detection systems and intrusion prevention systems. CSC will help the Air Force extend, operate and defend its portion of the Department of Defense network and provide full spectrum cyber capabilities for the Joint warfighter.
The Air Force Computer Emergency Response Team supports the 33rd NWS – the only operational unit in the Air Force tasked to provide 24/7/365 defense and monitoring of Air Force and United States Central Command worldwide classified and unclassified IP networks. The 33rd NWS provides network defense expertise and support to the Air Force Network Operations Commander, 624th Air Force Network Operations Center, Headquarters Air Forces Central, and field units throughout the Air Force.
CSC is Headquartered in Falls Church, Va., and has approximately 95,000 employees and annual revenues of $16.2 billion.














