IT management software provider ConnectWise on Friday announced updates that patch a critical vulnerability which, according to cybersecurity professionals, exposes thousands of servers to attacks.
The flaw, described as “improper neutralization of special elements in output used by a downstream component”, affects the ConnectWise Recover backup and disaster recovery product (v2.9.7 and earlier), and the R1Soft server backup manager (v6.16.3 and earlier).
The issue is a critical remote code execution vulnerability. The vendor has assigned it a priority rating of 1, which indicates that the vulnerability is either being targeted by hackers or it’s at high risk of being exploited in the wild.
ConnectWise Recover users have been urged to update to version 2.9.9, while R1Soft users should update to version 6.16.4.
The vulnerability was discovered by researchers at MDR company Huntress. Its CEO, Kyle Hanslovan, said Huntress could release details as early as Monday, but noted that ConnectWise’s patch is still being validated.
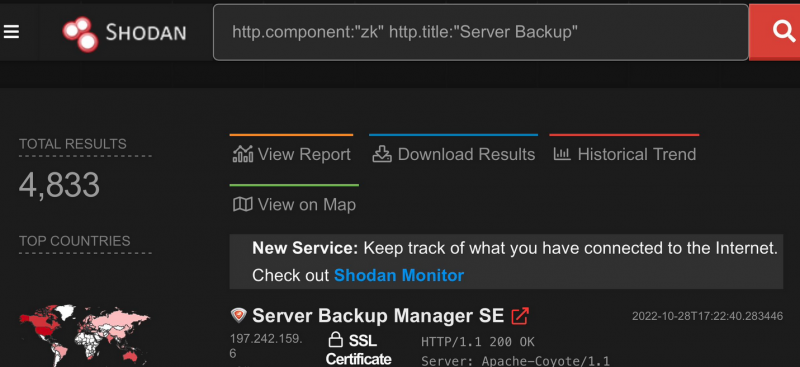
Hanslovan said Huntress researchers showed how they could push ransomware to nearly 5,000 internet-exposed R1Soft servers, many of which are located in North America and Europe. Hanslovan also confirmed potential supply chain impact considering that many of the affected systems belong to cloud hosting providers and MSPs.
Several members of the cybersecurity industry raised concerns about the existence of the vulnerability and the patch being announced on a Friday, which makes it more likely for affected servers to remain unpatched until Monday, leaving them exposed to potential attacks that could start over the weekend.
ConnectWise products have been known to be abused in ransomware attacks.
UPDATE: Huntress has published a blog post detailing its findings. The company says it’s not aware of in-the-wild exploitation, but its researchers developed PoC exploits to show how the vulnerability can be leveraged to bypass authentication, gain arbitrary code execution, and push the LockBit ransomware to all downstream endpoints.
Related: Vulnerability in BackupBuddy Plugin Exploited to Hack WordPress Sites
Related: Vulnerability Management Fatigue Fueled by Non-Exploitable Bugs
Related: Critical Vulnerabilities Patched in Veeam Data Backup Solution














