A new cloud security startup has emerged from stealth mode today, unveiling solutions specifically designed from the ground up to provide security for elastic cloud servers.
![]() CloudPassage, headquartered in Menlo Park, California, is looking to help companies manage their own cloud security by offering a single, purpose-built solution for the cloud that delivers multiple layers of defense for cloud servers.
CloudPassage, headquartered in Menlo Park, California, is looking to help companies manage their own cloud security by offering a single, purpose-built solution for the cloud that delivers multiple layers of defense for cloud servers.
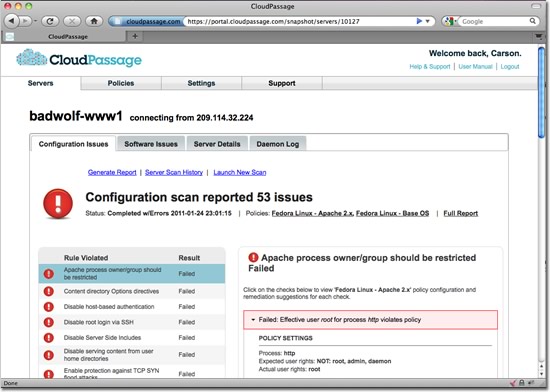
With the company launch, CloudPassage introduced its new line of server security and compliance products purpose-built for elastic cloud environments: Halo SVM (Server Vulnerability Management) and Halo Firewall.
Most compromises can be prevented by simple configuration changes, software patching or better firewall policies; but in an elastic cloud environment, the rate of growth and change are difficult for companies to manage.
The company’s Halo Firewall controls server attack surfaces by centralizing and automating host-based firewall management. The product provides customers with unified cloud-wide firewall policy management from a graphical web front-end, eliminating the untenable operational overhead and likely errors associated with manual host-based firewall management. Halo Firewall can automatically update individual host-based firewall configurations whenever cloud servers are added or removed – including server cloning or cloudbursting operations – with zero intervention by system administrators. It also helps address the issues of dynamic public-cloud IP addressing, a common firewall management complication cited by IaaS providers.
“Customers of our on-demand, enterprise-level email and social media marketing solutions have high standards for protecting their data and supporting their compliance needs,” said Tim McQuillen CIO and co-founder of StrongMail. “CloudPassage allows us to clearly communicate in exact technical terms how we secure our environments and deliver compliance verification as frequently as needed.”
The ability to create new servers in the cloud within seconds means IT departments can be faster and more agile, but it creates huge security problems. New copies of servers will duplicate all of the vulnerabilities and exposures that already exist, resulting in an increased attackable surface area on a company’s cloud server farm.
“Other server protection solutions that work in public clouds require painful deployment and management contortions,” said Carson Sweet, co-founder and CEO CloudPassage. “Because dozens of new servers can be created in seconds, through cloning and bursting, vulnerability and firewalling need to be done differently in the cloud; they need to be elastic.”
CloudPassage was co-founded by CEO Carson Sweet who previously served as the Principal Solutions Architect at RSA’s financial industry practice.
Read More on Cloud Security in SecurityWeek’s Cloud Security Section.













