Sonrai, a company that offers data and identity control solutions for cloud environments, on Tuesday emerged from stealth mode with $18.5 million raised in a Series A funding round.
Sonrai was founded in 2017 by Brendan Hannigan and Sandy Bird, who previously founded and worked for Q1 Labs, which IBM acquired in 2011 for its QRadar intelligence and analytics platform. Hannigan and Bird joined IBM Security following the acquisition, where they served as general manager and CTO, respectively.
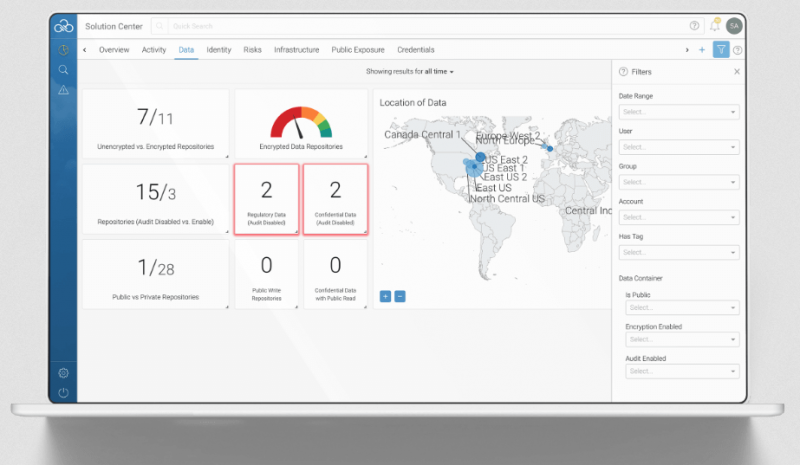
 Sonrai’s Cloud Data Control product, which the company built from the ground up, is a native cloud service that aims to provide organizations the discovery, mapping, classification and automation capabilities needed control data and users across their cloud environments.
Sonrai’s Cloud Data Control product, which the company built from the ground up, is a native cloud service that aims to provide organizations the discovery, mapping, classification and automation capabilities needed control data and users across their cloud environments.
Cloud Data Control works with cloud services such as AWS, Microsoft Azure and Google Cloud, and data sources using MongoDB, Elasticsearch, NoSQL, CouchDB and others.
According to Sonrai, its solution can help both DevOps and SecOps teams. The company says organizations can use it to assess and reduce risk, monitor usage and movement of data and users, and enforce accountability – all of these capabilities should help defend against external attacks and mitigate exposure caused by misconfigurations.
Cloud Data Control is also designed to help organizations ensure that they are compliant with regulations such as PCI-DSS, GDPR and HIPAA.
The list of benefits for DevOps teams, Sonrai claims, include the ability to integrate the service with their development frameworks via APIs, and the availability of analytics and views for cloud environments.
Hannigan, the CEO of Sonrai, told SecurityWeek that activation of the product takes only approximately 10 minutes and it does not require the installation of any new hardware or the deployment of an agent on endpoints. Deployment only involves setting up one “cloud monitor” (a Docker container) for each of the customer’s cloud providers. Sonrai says its product has already been tested and used by some organizations.
Hannigan says the service is available immediately worldwide. Pricing is based on the number of cloud providers, cloud accounts and data stores monitored by the service.
As for the funding, the Series A round was led by Polaris Partners and Ten Eleven Ventures – representatives from each of these companies will join Sonrai’s board of directors. Hannigan is an entrepreneur partner with Polaris Ventures.
Hannigan says the funding will be used to expand sales and further growth of engineering.
Related: CloudKnox Raises $10.8 Million to Help Manage Cloud Privileges
Related: Avanan Raises $25 Million in Series B Funding
Related: Orkus Exits Stealth Mode With Cloud Security Platform

