Cisco has informed users that a recently patched vulnerability affecting its Adaptive Security Appliance (ASA) and Firepower Threat Defense (FTD) software has been exploited in denial-of-service (DoS) attacks.
The vulnerability, tracked as CVE-2018-0296 and classified “high severity,” was addressed with the patches released by Cisco in early June.
The flaw was reported to the networking giant by researcher Michal Bentkowski, who discovered that a remote and unauthenticated attacker could gain access to sensitive system information through directory traversal techniques. Cisco’s own analysis of the bug revealed that it can also be exploited to cause impacted devices to reload and enter a DoS condition.
According to Cisco, the vulnerability exists due to the lack of proper input validation of the HTTP URL. An attacker can exploit the security hole by sending specially crafted HTTP requests to the targeted device.
The list of impacted devices includes 3000 series Industrial Security Appliances, ASA firewalls, and Firepower products.
Cisco updated its advisory last week to warn users that the vulnerability has been exploited to cause a DoS condition. The company noted that it has not seen any attacks attempting to leverage the flaw to obtain sensitive information.
“Cisco PSIRT has become aware of a public proof-of-concept exploit and is aware of customer device reloads related to this vulnerability. Cisco strongly recommends that customers upgrade to a fixed Cisco ASA software release to remediate this issue,” Cisco wrote in its advisory.
Bentkowski has made public the technical details of the flaw (blog post written in Polish) and at least two other researchers have published PoC exploits that can be used to obtain sensitive information, including usernames.
HackerOne’s Yassine Aboukir, who published a PoC on GitHub on June 21, noted that it’s easy to find vulnerable devices on the Internet using Shodan, Censys and even Google.
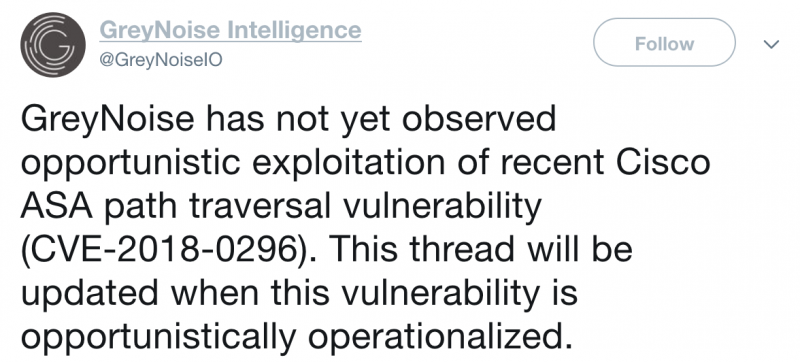
GreyNoise Intelligence has also been tracking exploitation of the vulnerability.
Related: Cisco Switches in Iran, Russia Hacked in Apparent Pro-US Attack
Related: Critical Flaws in Cisco DNA Center Allow Unauthorized Access
Related: Cisco Patches Critical Flaws in WebEx, UCS Director














