Centrify, a Santa Clara, Calif.-based provider of identity and access management (IAM) solutions, has teamed up with Bugcrowd for a public bug bounty program that offers researchers up to $3,000 per vulnerability.
Centrify has been running a private bug bounty program for the past two years, but it has now decided to allow all the 50,000 hackers on the Bugcrowd platform to find and report vulnerabilities.
The program covers the company’s main website, centrify.com, and its Identity Service and Privilege Service products.
The products are built on a cloud platform for which bug bounty hunters will have to register their own tenants for testing. The focus areas include web applications and the underlying REST API, and clients and installable agents.
Centrify said only its centrify.com website is in scope and bounty hunters have been instructed to focus on vulnerabilities exploitable in current web browsers and user authentication flaws. Subdomains or related hosts are not covered, but centrify.force.com/partners, centrify.force.com/support and partners.centrify.com can be tested for privilege escalation.
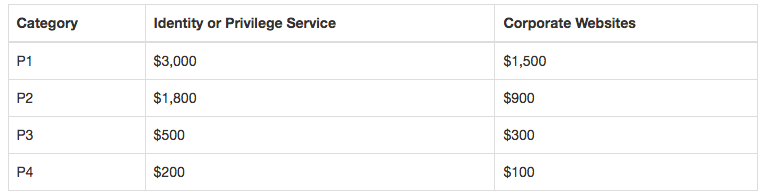
Researchers can earn the top rewards – $3,000 for flaws in the Identity and Privilege products and $1,500 for flaws in the corporate website – if they find vulnerabilities that have a P1 priority rating. This includes critical server misconfigurations, server-side injections, broken authentication and session management, sensitive data exposure, and cryptographic issues.
The least serious vulnerabilities affecting Centrify products can earn researchers $200, or $100 if they affect the company’s website.
“As a leader in identity services, it is incumbent upon us to fully vet the security on our platform to ensure that each user’s access to apps and infrastructure is secure and that we continue to deliver the best solutions,” said Raun Nohavitza, Senior Director of IT at Centrify. “Bugcrowd’s platform, organization, experience with triage and relationship with the security community make their bounty program very attractive. With Bugcrowd we’re not only doing the right thing for our security offerings in the best way possible, but we’re also getting consistent administration and management for our ongoing program.”
Related: Centrify Raises $42 Million to Expand Identity Management Business
Related: Identity Management Firm Okta Launches Bug Bounty Program












