Canonical, the company behind the Ubuntu operating system, confirmed over the weekend that one of its GitHub accounts was hacked.
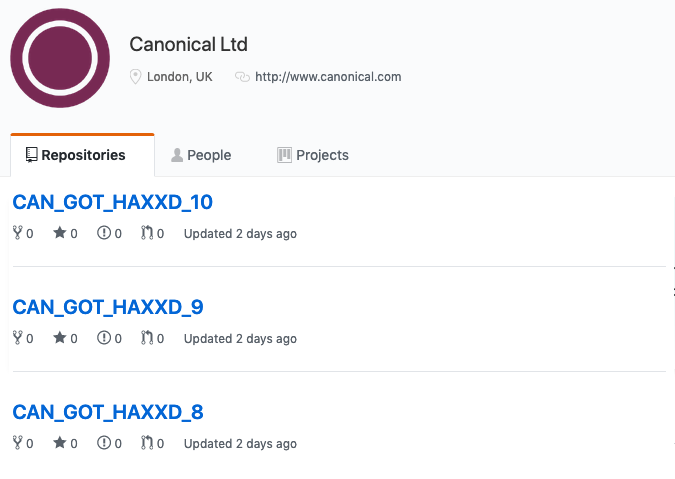
According to Canonical, the attacker hijacked the account on July 6 using compromised GitHub credentials. The hacker used the access to conduct various activities, including to create repositories and issues.
Shortly after the breach was discovered, Canonical removed the compromised account from its organization in GitHub. The investigation is ongoing and the company has promised to provide more details after it’s completed, but so far there is no evidence that the incident impacts source code or personally identifiable information.
“Furthermore, the Launchpad infrastructure where the Ubuntu distribution is built and maintained is disconnected from GitHub and there is also no indication that it has been affected,” Canonical stated.
This incident appears to be far less serious than the breach of the Ubuntu Forums back in 2016, when a hacker exploited a known SQL injection vulnerability in one of the add-ons installed on the site and gained access to data belonging to over 2 million registered users.
Canonical is not the only Linux maker whose GitHub account was targeted in recent years. Roughly one year ago, a GitHub account of the Gentoo Linux distribution was hijacked. In that incident, the attackers planted malicious code and attempted to lock out Gentoo developers from the compromised account.
Related: Arch Linux AUR Repository Compromised
Related: Hard-Coded Credentials Found in Alpine Linux Docker Images













