A new survey of managers and executives revealed that organizations are all talk and no walk when it comes to risk-based security management, as most have not implemented a formal program to manage risk.
According to research by Tripwire and the Ponemon Institute, security spending within organizations is not aligned with perceived risk. Organizations are making excellent progress with deploying preventive controls, but are not implementing detective controls, the survey found. In fact, for organizations in the United States, 80 to 90 percent said they have partially or fully deployed preventative controls, but only 50 percent have deployed the majority of detective controls, according to Tripwire. As a result, the organizations are unable to identify, implement, and continuously monitor their programs effectively.
The State of Risk Based Security Management (RBSM) study found that many organizations are relying on cost reductions to gauge the success of RBSM programs. Such a metric can “encourage the wrong behavior and actually increase the risk,” Tripwire said.
“We believe risk-based security management will transform organisations’ approach to protecting critical information assets and technologies from one that is reactive to proactive,” said Larry Ponemon of the Ponemon Institute.
Although organizations claim to be strongly committed to RBSM, they aren’t taking action, the survey found. Over 72 percent of UK organizations claimed a “significant” or “very significant” commitment, but more than half of the surveyed organizations didn’t have formal strategies or procedures in place to manage risk. The numbers are similar for US organizations, with 77 percent expressing a strong commitment, but only 52 percent adopting a formal approach. Only 46 percent have actually deployed any RBSM activities, according to the survey.
This gap creates potential risks for businesses moving forward, Tripwire said.
“Savvy security executives will leverage risk as a means to drive business-relevant discussions, and use objective measures to show security effectiveness. It is imperative to break the cycle of ‘habitual security spending’ to better align security resource allocations within their businesses,” said Dwayne Melancon, CTO for Tripwire.
The survey collected information from 2,145 individuals from organizations of different sizes and types in the United Kingdom, Germany, Netherlands and the United States. The respondents were asked how they viewed risk-based security management within their organizations, how they addressed the risks, and how they measured the effectiveness of the measures deployed.
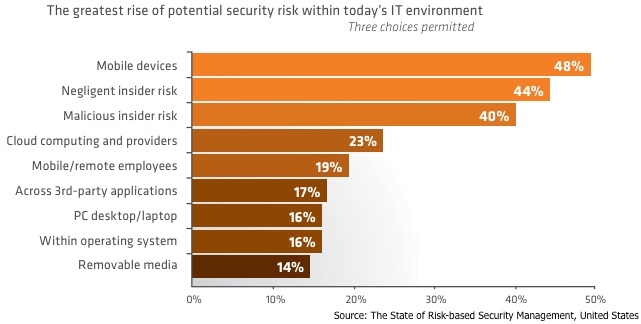
Perceptions of RBSM differed in the US, UK, Germany and the Netherlands, the survey found. In the US, 71 percent of organizations said they were concerned about malicious insiders, compared to 49 percent in UK, 32 percent in Germany, and only 16 percent in the Netherlands.
Tripwire actually released U.S. results earlier in June during the Gartner Security & Risk Management Summit. About 30 percent of organizations in the US had no RBSM strategy, and about 23 percent had an informal or ad-hoc strategy, Tripwire said.
“It is evident from this data that CISO’s must to move beyond ‘lip service’ when it comes to Risk-Based Security Management,” said Melancon.
The full report is availble here.











