Bit9 has launched a free tool that scans for executable files (dll, installer, script and other programs) on Windows-based systems to help users detect potentially malicious files and identify areas of risk on their PCs.
Dubbed the Bit9 Trust Assessment Tool (TAT), the utility evaluates the files based on numerous factors, including their age, prevalence, publisher, source, AV scan results, and other key indicators to determine a trust rating for the machine, the company said.
TAT runs on versions of Windows XP or later and scans files with potentially executable code and sends the inventory of files to the Bit9 Cloud Services for analysis. From there, Bit9 anonymously aggregates the results and provides users with a report of the trust rating of their PC and areas of risk.
According to the company, the Bit9 Trust Assessment Tool will:
· Identify all software installed and running on a PC, including any executable, .dll, installer, script and other programs
 · Highlight files or processes that exhibit behaviors or properties common to advanced threats
· Highlight files or processes that exhibit behaviors or properties common to advanced threats
· Provide an overall trust rating for the PC by analyzing all executable code in system files
Reports generated by the Bit9 Trust Assessment Tool include:
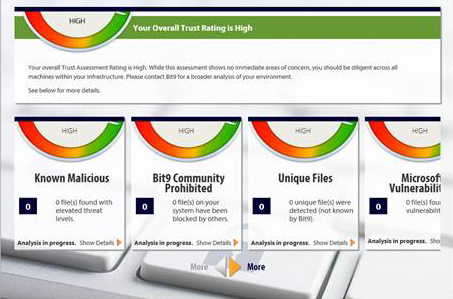
· Top-level trust assessment: Aggregates trust levels from the various file categories to provide an overall trust assessment rating
· Known malicious files: Indicates if any files have known vulnerabilities or are recognized as malware
· Advanced Threat Indicators: Behaviors observed that may indicate a machine is compromised
· Unique Files: Files that have not yet been seen across the Bit9 Trusted Community
· Community Prohibited: Files that have been blocked by a number of enterprise Bit9 admins throughout the Bit9 Trusted Community
“The first step in securing an enterprise endpoint is knowing what’s running on it,” said Brian Hazzard, vice president of product management for Bit9. “We developed this powerful Threat Assessment Tool so users can see if their machine contains untrustworthy software that exposes them to potentially devastating cyber threats. Unlike typical virus scans that only look for known malware and miss many of today’s advanced threats, the Bit9 TAT performs a comprehensive analysis of all software on a PC and provides an overall trust rating.”
The Bit9 TAT can be downloaded here.
















