Google is reported to have “declared war on the password”. While we all just hate passwords and “a quick tap on your computer with the ring on your finger” sounds like a much cooler way to login, making changes in a fundamental mechanism such as authentication should be thoroughly and carefully considered.
The proposed changes, along with their merits, may carry some serious implications, especially on end-users’ privacy. These concerns are heightened when the initiative originates from a commercial party, which its business model is mostly based on utilizing end user’s data for the sake of more effective advertising campaigns.
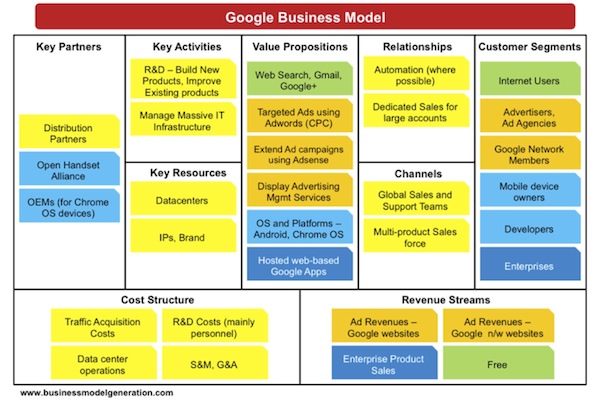
Figure 1 According to bmimatters.com, Google generates over 96% of its revenues from advertising
Google’s “password killer” initiative
Stealing passwords is often an important milestone in a hacking campaign, as passwords provide access to secret data which is the end goal of the attackers. In order to maliciously obtain passwords attackers may abuse either client side vulnerabilities with a password stealing malware, server side vulnerabilities by hacking into the database where passwords are stored, or “user-side” social vulnerabilities with phishing sites. In an article named “Authentication at Scale” (The article is behind the paywall of “IEEE Security & Privacy” magazine ), Google’s researchers suggest a “Device-Centric Authorization” to mitigate many of these threats:
“Imagine … that each client device you own had its own strongly asserted identity. When you acquire a new device, you “bless” it with the ability to access your account. This delegation step might require the device to submit multiple factors on your behalf the very first time, or might require an out-of-band pairing protocol. From then on, the device always asserts its unique credential to server. As a result of this delegation, your device (or your well-isolated profile on a shared device) is permanently granted access to your data.”

Figure 2 Physical USB token
The proposed solution is said to increase the end user’s privacy, as “the secure element never returns a previously generated public key in any new registration step. This makes it hard to track a user across websites by using the token as a super-cookie that bypasses other anonymizing precautions.”
Increasing the end-users’ privacy is an admirable cause, but Google didn’t seem to be so interested with it when it came to implementing the “Do Not Track” feature. The Do Not Track (DNT) is a proposed HTTP header field that requests that a web application disable its tracking of an individual user. Google’s Chrome was the last major browsing platform to support the feature .
An alternative explanation to Google’s motivation
Creating a complete customer profile is the holy grail of advertising, allowing advertisers to invest their advertising budget only in the relevant target audience. However, establishing such a profile of the user’s activities across websites is not an easy task, as the user may use a different username for each application or would prefer to remain anonymous to the website due to the annoying registration process.
By “magically blessing” a device to authenticate on the user behalf many of these problems are solved, as the registration and authentication involve a significantly smaller effort for the user on one hand and associates a unique identification with the user across different devices and services on the other hand. And the best part – the implementation disables other sites from establishing the same identity via a “super cookie”, leaving that knowledge only the device itself which is, of course, created by Google and therefore may expose the information exclusively to Google and its advertising customers.
If you think this explanation of Google concealing a move aimed to gain a competitive advantage as a move aimed to increase end users privacy to be a farfetched one, consider the following case. More than a year ago, Google switched its search functionality to be under SSL encryption. A consequence of this move was the blocking of the transfer of the HTTP referrer information which includes the search terms used by the user to the referred websites. However, Google made that information available for its true customers, the advertisers. In the words of the “search engine guru”, Danny Sullivan:

Figure 3 Google search switch to SSL blocks search term from target website (unless it’s an advertiser)
“So why do it? One reason is that it makes Google more competitive. If someone lands on your web site, and you know the search term they used, you can then target them in various ways across the web with ads you believe reflect that search interest. All you need is the initial term. This is called “retargeting,” and Google’s a leading provider of retargeted ads. When you cut the referrers out, except for your own advertisers, Google makes it harder for its competitors to offer retargeting services.
Another benefit is that it prevents anyone but Google’s own advertisers from doing keyword-level conversion tracking. With search referrers, you can determine what someone who searched for a particular term later did on your site. What further pages did they go to? Did they purchase a product or service? Without the search terms, you can’t do this degree of analysis. That is, of course, unless you buy an ad. Conversion tracking at the keyword level turns into another sales feature for Google.”
The price of privacy is eternal vigilance
The technological version of the “There ain’t no such thing as a free lunch” adage claims that “If you use a tech service for free then product is you”. Google is not “Scroogling” their end users, as their competitors would like us to believe. They just want to provide value for their true customers, the advertisers, by selling them a good product: data on the non-paying end-users.
Therefore, when it comes to setting the standards for crucial internet functionality such as authentication, the Internet community must remain vigilant and carefully examine and scrutinize change proposals, to ensure they support the greater good of all of the Internet users.

