Some form of malicious activity was detected on roughly one-third of the industrial control system (ICS) computers monitored by Kaspersky in the first half of 2021.
In its latest ICS threat landscape report, Kaspersky reveals that the overall percentage of attacked devices only rose by 0.4 percentage points, but in some countries the increase was more significant.
An increase of more than 10 percentage points was observed in Belarus, where roughly half of the devices monitored by Kaspersky were attacked, and Ukraine, where 33% of devices were attacked. Belarus and Ukraine, along with Russia, were the countries that saw the most significant increase in terms of threats from the internet.
Political relations have been tense in the region, but, when asked by SecurityWeek, Kaspersky could not say whether the increase in attacks had any connection to the political situation.
A significant increase in the percentage of attacked computers was also observed in Australia and Hong Kong, and these countries are no longer among the top 10 “safest” countries.
Overall, threats from the internet were blocked on roughly 18% of devices monitored by the cybersecurity firm. In comparison, threats delivered through removable media were observed on 5% of devices, and malicious email attachments were blocked on 3% of computers.
Industrial systems from which the company collected data include SCADA servers, historians, OPC systems, engineering and operator workstations, HMIs, computers used to manage industrial networks, and devices that are used to develop industrial automation software.
In terms of the targeted industries, the most affected in the first half of 2021 were building automation, engineering and ICS integration, oil and gas, energy, and automotive manufacturing.
Kaspersky said its products blocked a total of more than 20,000 malware variants belonging to approximately 5,000 malware families. In the case of the variants blocked in H1 2021, the number is roughly the same as in the two previous years.
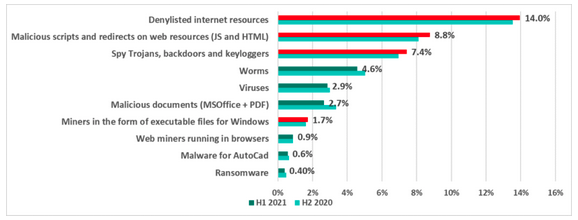
There haven’t been any significant changes compared to the previous six months in terms of the types of malware. Ransomware was blocked on 0.4 of devices, with the most common detections being for blacklisted internet resources, malicious scripts and redirects, and trojans, backdoors and keyloggers.
“Industrial organizations always attract attention from both cybercriminals and politically-motivated threat actors,” said Evgeny Goncharov, security expert at Kaspersky. “Reflecting on the previous half year, we have seen among other findings, growth in the number of cyberespionage and malicious credential stealing campaigns. Their success has most likely been the main factor raising the ransomware threat to such a high degree, and I see no reason why some of the APT groups won’t benefit from these credential stealing campaigns as well.”
Related: Kaspersky Sees Rise in Ransomware Attacks on ICS Devices in Developed Countries
Related: Pandemic Leads to Rise in Industrial Systems Targeted Via RDP: Report















