
Researchers at FireEye have discovered backdoored versions of a popular ad library in thousands of iOS applications, including ones published in the Apple App Store.
According to the security firm, the library opens a backdoor on the device running the affected iOS application, allowing malicious actors to gain access to sensitive data and device functionality. Attackers could control the backdoor remotely by loading JavaScript code from a server.
The library in question is a version of the mobiSage software development kit (SDK) from the mobiSage mobile ad network of adSage, a China-based advertising technologies and services provider that has offices in the United States. According to the company’s website, mobiSage is the most influential ad network in China, covering nearly 90 percent of the country’s mobile device users. The mobiSage SDK is used by developers to display ads in their applications.
FireEye has determined that the backdoor is present in versions 5.3.3 through 6.4.4 of the ad library, but it does not exist in the latest version, 7.0.5. The security company has identified 17 different versions of the backdoored ad library, which it has dubbed “iBackDoor.”
The problematic versions of the library have been identified in a total of 2,846 iOS applications, which have made more than 900 attempts to contact an ad server that can be used to deliver the JavaScript code necessary to control the backdoor.
FireEye has not seen any malicious activity associated with the ad server, but the threat can be leveraged to carry out a wide range of tasks. The list includes capturing audio and screenshots, manipulating files in the app’s data container, monitoring device location, reading, writing and resetting the app’s keychain, uploading encrypted data to a remote server, side-loading unauthorized apps by prompting the victim to click an install button, and opening other applications present on the device.
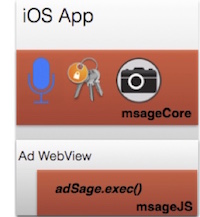 Such attacks are possible due to two key components of the mobiSage library: msageCore, an Objective-C component that implements the backdoor’s underlying functionality, and msageJS, a JavaScript component that can trigger the backdoors using interfaces exposed by msageCore via a WebView.
Such attacks are possible due to two key components of the mobiSage library: msageCore, an Objective-C component that implements the backdoor’s underlying functionality, and msageJS, a JavaScript component that can trigger the backdoors using interfaces exposed by msageCore via a WebView.
“While we have not observed the ad server deliver any malicious commands intended to trigger the most sensitive capabilities such as recording audio or stealing sensitive data, affected apps periodically contact the server to check for new JavaScript code,” FireEye has warned. “At any time, malicious JavaScript code that triggers the backdoors could be posted, and it eventually would be downloaded and executed by affected apps.”
Apple was informed about the risky ad library on October 21, FireEye said. adSage has not responded to SecurityWeek’s request for comment by the time of publication.
This is not the first time an SDK offered by a Chinese company has put mobile users at risk, but previously reported incidents mainly affected Android device owners.
Last month, Palo Alto Networks reported spotting 18,000 Android applications capable of stealing SMSs from phones. All of the affected apps had been built using an SDK from the Chinese mobile ad platform Taomike.
Another recent incident involves the Moplus SDK from the Chinese Internet company Baidu. Researchers found a series of backdoor routines allowing attackers to push phishing pages, send fake SMS messages, upload files from the device to remote servers, install apps on the device, and insert arbitrary contacts.
















