New Research Shows Cybercriminals Moving Operations to Canada
Could the recent takedowns of the Rustock and Coreflood botnets by U.S. authorities be triggering a change in infrastructure operations for cybercriminals? That may be the case, according to recent insights and data coming from security firm, WebSense.
Cybercriminals are always looking for the best places to house their infrastructure. And, this time, Canada appears to be the prime target in terms of locations being used to host malicious content. Data from IP addresses in China and Eastern Europe are highly scrutinized and undergoing intense evaluation, often increasing the chances of a red flag being raised and being blocked by security gateways. So cybercriminals are on a quest to move their networks to countries, like Canada, that have better cyber reputations—giving them a better chance at success and longer lasting campaigns.
According a recent report from the APWG, the average uptime of a phishing campaign during the second half of 2010 was 73 hours, the longest average for any time period since it began tracking uptime three years ago. When it comes to the success of a phishing campaign the “uptime” or “live” times of phishing attack are a vital measure of how damaging phishing can be. The longer a phishing attack remains active, the more damage can be done.
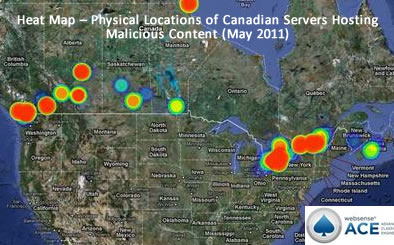
Current trends are pointing to Canada as the new breeding ground for cyber criminal activity, with more malicious content being hosted in Canada than ever before. According to WebSense data:
· 319% Jump in Hosted Phishing Sites – Canada saw a huge increase in the number of servers hosting phishing sites, jumping 319 percent in the last year. This tremendous increase over the last 12 months is second only to Egypt in terms of the growth of sites hosting crime ware.
· 53% Increase in Bot Networks – Cyber criminals are moving their command and control centers to safer grounds. In the past eight months, Canada saw a 53 percent increase in bot networks. Canada is the only country that showed an increase in bot networks over the last eight months, when compared to the countries above.
· Overall Increase in Cyber Crime – In 2010 Canada was #13 in the world for hosting cyber crime, and in 2011 Canada jumped to #6!
| 2011: Jan-May | 2010: Jan-May |
|
1. United States 2. France 3. Russia 4. Germany 5. China 6. Canada 7. Netherlands 8. South Korea 9. Romania 10. UK
|
1. United States 2. Russia 3. Germany 4. France 5. China 6. Netherlands 7. UK 8. South Korea 9. Turkey 10. Australia 11. Poland 12. Czech Republic 13. Canada |
“More malicious content is being hosted in Canada than ever before,” said Patrik Runald, senior manager of Security Research, Websense. “Cyber criminals are taking advantage of Canada’s clean cyber reputation, and moving shop. We’re seeing all time highs for both hosted phishing sites and bot networks.”















