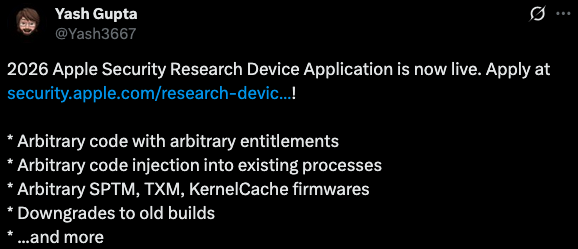
Apple has kicked off the application period for the 2026 Security Research Device Program.
White hat hackers interested in obtaining an iPhone that was specifically configured for security research can apply until October 31. Apple has been offering these ‘hackable’ iPhones to security researchers since 2020.
Through the Security Research Device Program, or SRDP, eligible researchers receive an iPhone that enables iOS security analysis without the need to bypass the security features that are enabled on a regular phone.
Those who are accepted into the program are given shell access to run any tools, and they get early previews of software and security projects, as well as special tools to aid their work.
The iPhones distributed as part of the SRDP are given to researchers under a 12-month renewable loan agreement and they are not meant for personal use.
Apple says only researchers who “have a proven track record of success in finding security issues on Apple platforms, or other modern operating systems and platforms” are eligible.
The discovered vulnerabilities qualify for a reward under Apple’s bug bounty program.
The tech giant rarely shares payout data from its bug bounty program, but when it announced the SRDP for 2024, Apple revealed that it had rewarded over 100 reports from SRDP researchers, with multiple $500,000 rewards and a median of nearly $18,000.
Apple’s SRDP page does not specify which iPhone model will be handed out as part of the 2026 program, but the most likely candidates are the iPhone 16 or the upcoming iPhone 17, which is set to become available later this month.
Related: WhatsApp Zero-Day Exploited in Attacks Targeting Apple Users
Related: Apple Patches Zero-Day Exploited in Targeted Attacks
Related: Gabbard Says UK Scraps Demand for Apple to Give Backdoor Access to Data


