Apple has launched a new security research blog and website, which will also be the new home of the company’s bug bounty program.
The tech giant has taken the opportunity to reveal that it has paid out a total of $20 million through its Apple Security Bounty (ASB) program. The average reward in the product category is $40,000, and more than 20 separate payouts for high-impact vulnerabilities exceeded $100,000.
Apple announced a private bug bounty program for iOS in 2016 and a public program covering all of its major software and operating systems in 2019.
In comparison, Microsoft has been paying out more than $13 million every year for the past three years, totaling more than $40 million between July 2019 and July 2022. Google said in July 2021 that it had paid out more than $29 million in the past 10 years and this year it reported awarding a record $8.7 million in 2021 alone.
Facebook has paid out a total of $14 million since 2011. Zoom awarded approximately $1.8 million through its bug bounty program in 2021.
The new Apple Security Research website can be used to report security and privacy issues to Apple, as well as to keep track of their status and communicate with the company.
While there have been many complaints from the security research community regarding Apple’s bug bounty program, the tech giant says it has made improvements. This includes completing initial vulnerability report evaluations faster and making it easier for researchers to report issues and communicate with its teams.
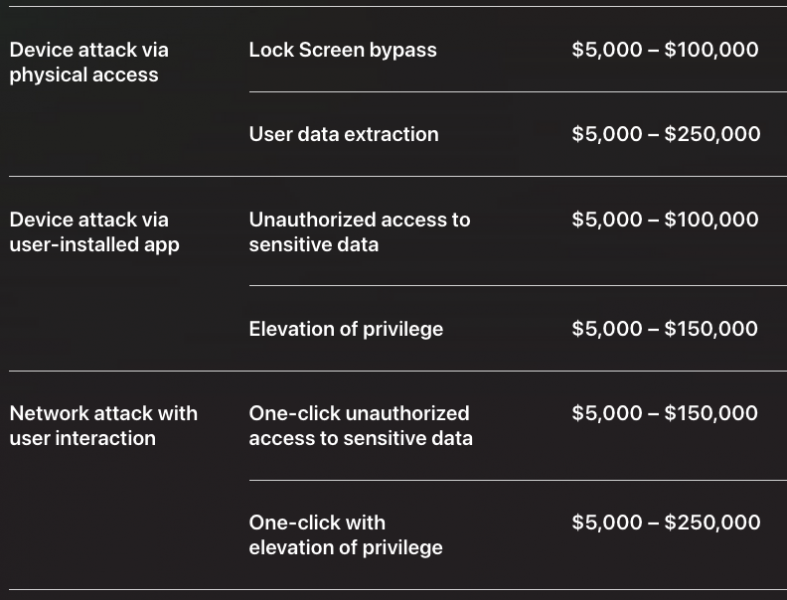
With the new site, Apple is also providing more detailed information on the reward ranges for each product and service. For instance, a device attack via physical access that results in user data extraction can earn up to $250,000. A network attack without user interaction that results in kernel code execution with persistence is worth up to $1 million.
Beta software issues have a maximum bounty of $1.5 million, while a Lockdown Mode protection bypass can earn a researcher up to $2 million.
In the case of vulnerabilities affecting Apple services, the top reward is $100,000, which can be earned for iCloud hacks.
The Apple Security Research website will also provide the research community with technical details on its security technologies. The first technical post published on the website delves into memory safety upgrades in XNU, the kernel at the core of iPhone, iPad, and Mac devices.
Apple also announced that it’s accepting applications for the 2023 Apple Security Research Device program until November 30. As part of this program, researchers are provided a special iPhone that allows them to conduct research without the need to bypass its security features.
*updated information on Facebook bug bounty payout
Related: Apple Patches New macOS, iOS Zero-Days
Related: Apple Pays Out $100,000 for Webcam, User Account Hacking Exploit
Related: Apple Security Flaw: How do ‘Zero-Click’ Attacks Work?












