Apple has extended its two-factor authentication (2FA) feature to the FaceTime and iMessage communication services to allow users to protect their accounts and their data.
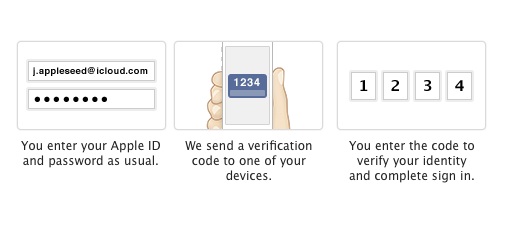
Passwords are often stolen by malicious actors and many major companies have realized that an additional layer of security is needed to protect accounts. With 2FA enabled, users will be required to provide their password and a 4-digit verification code when they log in to their accounts from an unrecognized device. This way, if the password is compromised, an attacker will not be able to access the account.
The verification code is delivered via SMS or the Find My Phone service to a trusted device registered by the user. At least one SMS capable phone number must be registered.
Customers are also provided with a 14-character recovery key that they can use to regain access to their account in case they lose their trusted device or forget their password.
Apple introduced two-step verification for Apple IDs in March 2013 following the hack attack targeting journalist Matt Honan. Last year, in response to the celebrity picture leaks, the company extended the option to iCloud.
In order to enable 2FA for their accounts, Apple customers must go to My Apple ID, sign in to their accounts, select Password and Security, and select Get Started under Two-Step Verification. FaceTime and iMessage users who previously enabled 2FA don’t have to take any action.
2FA can be highly useful for protecting accounts against unauthorized access, but the security feature can sometimes be bypassed. Last summer, researchers found a way to bypass PayPal’s 2FA.











