Password proliferation is bad, for many, many, many reasons. But the worst reason is that people tend to re-use passwords all over the place. It’s difficult if not impossible to keep all the various passwords straight that you need to bank, shop, do just about anything on the internet these days.
It turns out there is a better way to handle authentication than having individual usernames and passwords for every online account: federated login through massive consumer sites like Facebook, Google and Twitter and Yahoo!.
All of those “Login with Facebook” and “Login with Your Twitter ID” buttons across the Internet let people create accounts at a third party website via the OAuth protocol without surrendering their password. And these third party sites have accountability with the OAuth providers to not abuse the information they receive. Yes, in the early days of OAuth, there were some cases of abuse, such as harvesting and misusing friend lists, but today most OAuth clients just get your email address, which is all they really need to uniquely identify a consumer.
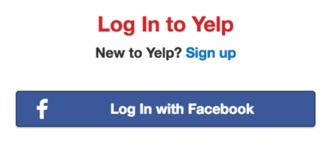
In theory, a website could offer federation login via dozens of OAuth-providing social media sites. But in reality, a website designer really just wants to support the handful of mega sites like Facebook and Google that represent the largest number of users. For example, today Yelp offers federated logins only through Facebook.
This brings us to Yahoo!. The leak of half a billion user credentials is, of course, a big deal in and of itself, but another potential loss is the decrease in federated login options for consumers. After this breach, it’s likely we’ll be seeing fewer and fewer “Login with Yahoo!” buttons across the Internet.
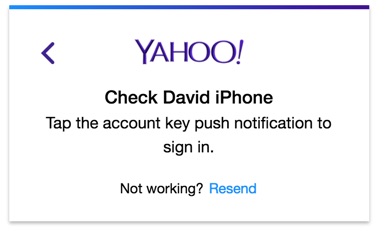
And that’s too bad, really, because Yahoo! was trying to do some cool stuff with password-less authentication. The new(ish) Yahoo Account Key feature let users authenticate via a press of a button on their mobile phone rather than entering a password.
Given its still-enormous user base, the loss of a Yahoo! as a source of federated logins could be detrimental to the Internet. If Yahoo! does in fact get removed from the short list of OAuth identity providers, then that leaves just two mega sites: Google and Facebook. If either of these suffer a massive breach, then we’d be down to just one giant repository of consumer identities, and that is too few.











