Adobe on Thursday released a second fix for the Reader vulnerability tracked as CVE 2019-7089 after the researcher who discovered the flaw managed to bypass the first patch.
The security hole, identified by Alex Inführ from Cure53, allows a specially crafted PDF document to send SMB requests to the attacker’s server when the file is opened.
The vulnerability, similar to CVE-2018-4993, allows a remote attacker to steal a user’s NTLM hash included in an SMB request, and it can be leveraged to alert an attacker when their malicious PDF document has been opened by the targeted user.
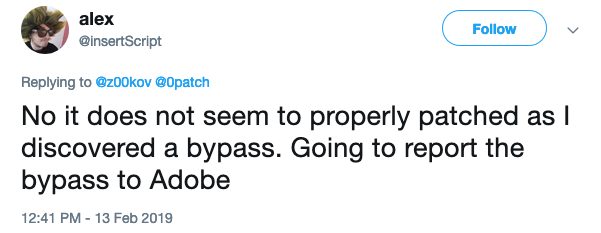
Adobe released a fix for CVE 2019-7089 with its February 2019 Patch Tuesday updates, but Infuhr quickly discovered that it could be bypassed.
Adobe has now released another update for Reader in an effort to address the flaw, which it has described as a critical information disclosure issue. The company has assigned a new CVE identifier, CVE-2019-7815, to the vulnerability.
It’s worth noting that Infuhr had made his findings public more than two weeks before Adobe released the first patch. An unofficial fix was released by 0patch one day before Adobe’s official patch came out.
It’s also worth mentioning that CVE 2019-7089 was the second flaw patched by Adobe that was similar to CVE-2018-4993.
Despite details of the security hole being public for several weeks, Adobe says it’s not aware of any in-the-wild exploits. The company has assigned it a priority rating of 2, which indicates that exploitation should not be imminent.
Related: Two Critical Flaws Patched in Adobe Acrobat, Reader
Related: Flash Player Update Patches Disclosed Code Execution Flaw
Related: Adobe Patches Information Disclosure Flaws in Experience Manager














