Adobe this week announced the open-source availability of ‘One-Stop Anomaly Shop’ (OSAS), a new tool designed to help security teams discover anomalies in datasets.
Building on previous research, white papers, and other projects from Adobe’s Security Intelligence Team, OSAS out-of-the-box allows researchers to experiment with datasets, control data processing and feature combining, and help identify a solution for detecting security threats.
The new open-source project tackles the issue of data sparsity, which may appear when using machine learning (ML) algorithms and models with security logs that present a large feature-space, in which case previously unseen examples may be poorly handled.
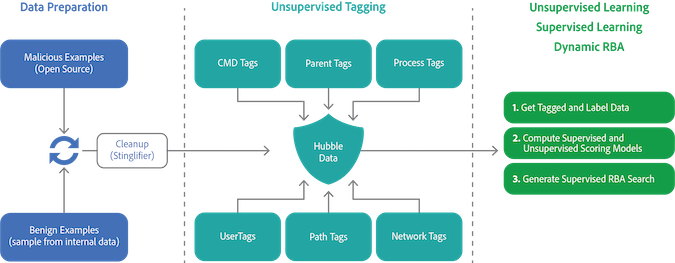
To reduce this effect, OSAS implements a two-step approach to data processing, where raw data is first consumed and tagged based on standard recipes (and complex features are also created), and labels are then used as input features for both supervised and unsupervised ML algorithms.
A command-line interface (CLI) tool, OSAS currently can be used to automatically generate a custom pipeline configuration file, to create a pre-trained model for the custom pipeline, and to apply the created model on previously unseen data.
Courtesy of an automatic learning/tagging function, OSAS can be used on a variety of datasets and projects, while the “Expert Knowledge Based” tagging component allows for the targeting of security threats, in a semi-supervised learning operation, similar to a “Risk Based Alerting” model.
Adobe has made the full source code of the project available on GitHub, alongside a dockerized variant that features a WebUI and ElasticSearch OpenDistro integration.
Related: The ‘Katz’ Out of the Bag: Catching Mimikatz With Anomaly Detection
Related: Google Releases Beta of Anomaly Detection for G Suite Customers
Related: IBM Releases Open Source Toolkits for Processing Data While Encrypted







