As anticipated, Adobe has released security updates for Acrobat and Acrobat Reader Products. These updates are classified as critical as the vulnerabilities could cause the application to crash and could potentially allow an attacker to take control of the affected system.
Adobe recommends users of Adobe Reader 9.3.1 and earlier versions for Windows, Macintosh and UNIX update to Adobe Reader 9.3.2. (For Adobe Reader users on Windows and Macintosh, who cannot update to Adobe Reader 9.3.2
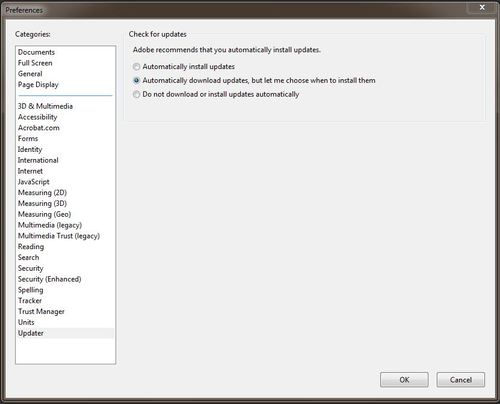
The new version includes a new automatic software update feature, allowing automatic updates on a regular schedule or allowing users to install updates manually.
More Information is available on Adobe’s Website:
http://www.adobe.com/support/security/bulletins/apsb10-09.html
Users can also proceed directly to the download page for the updates:
Adobe Reader users on Windows can find the appropriate update here:
http://www.adobe.com/support/downloads/product.jsp?product=10&platform=Windows
Adobe Reader users on Macintosh can find the appropriate update here:
http://www.adobe.com/support/downloads/product.jsp?product=10&platform=Macintosh
Adobe Reader users on UNIX can find the appropriate update here:
ftp://ftp.adobe.com/pub/adobe/reader/unix/9.x/9.3.2/. Acrobat Security Settings