Variant of Popular ZeuS Malware Targets U.S. Military Around the World
Malware created with the ZeuS toolkit is targeting members of the U.S. military with an email asking them to update their account information online.
Members of the U.S. Military have been receiving emails similar to the following: Targets of this scam will receive an email with the following text:
Dear Bank of America Military Bank customer:
This letter is to inform you that there is an update required for your Bank of America Military Bank Account, for this reason your account has been flagged.
In order to update your account, please follow this link.
Thank you for banking with us!
Bank of America Military Bank accounts support.
Robert McArdle, Advanced Threats Researcher at Trend Micro in a blog post noted, “Should the recipients click the link, they will be brought to a page that is almost identical to the real login page of the bank. However, this fake login page is actually hosted in Russia.”
No matter what user name and password entered by the victim, they are taken to a page, which contains the Update Tool malware that is says users must install in order to prevent their banking account from being locked.
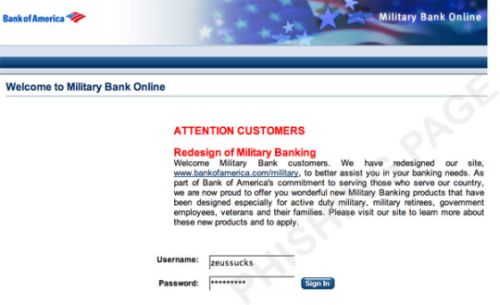
Image Credit: Trend Micro Blog
UpdateTool.exe is a ZeuS variant identified by Trend Micro as TSPY_ZBOT.BIZ. Unfortunately, when Zeus infects PCs, users rarely notice any harm, and those who click on a link will may even have a chance manually download the executable file, as the malware first runs a series of browser exploits.
ZeuS, also known as Zbot, WSNPOEM, NTOS and PRG, is the most prevalent banking malware platform for online fraud, and has been licensed by numerous criminal organizations. The program then waits for the user to log onto a list of targeted banks and financial institutions, and then steals login credentials and other data which are immediately sent to a remote server hosted by cybercriminals. It can also modify, in a user’s browser, the genuine web pages from a bank’s web servers to ask for personal information such as payment card number and PIN, one time passwords, etc.
McArdle also made note of similar attack last year – “At that time, it used a fake Facebook login page as bait. However, it also used a file called UpdateTool.exe and told users they needed to install it to access their accounts, which was also a ZeuS variant. All of these show that perhaps the same gang is behind the current wave of attacks.”
Anti malware detection of ZeuS has a poor track record. In a 2009 report based on information gathered from 3 million desktops in North America and the UK Trusteer found that the majority of ZeuS infections occur on antivirus protected machines. Specifically, Trusteer found that among Zeus infected machines 55% had up-to-date Antivirus protection installed. The population of machines infected with ZeuS is enormous — one in every 100 computers according to Trusteer research.















