16 Years of Black Hat, 16 Years of Attacks: What Enterprises Can Learn from the History of Attacks
The annual Black Hat convention always seems to mark turning points in cybersecurity, and this year was no exception. More than ever before, though, it signaled a major shift. NSA Director General Keith Alexander elevated “cybersecurity” from a skill practiced by ultra-technical professionals and hackers to a wide-spread geopolitical and commercial issue with massive exposure that now touches the lives of everyone.
Despite the political hoopla, Black Hat’s technical roots were still much in evidence. The items that received the most attention were the many revelations, discoveries and “Black Hat” findings that always make the event one of the most anticipated security gatherings year after year. Everything from weaknesses found in mobile communications to attacks on SSH and the latest in spear phishing have resonated through the headlines.
As Black Hat celebrated its Sweet 16, we decided to take a look at how the threat landscape has changed over the years and what the security community could learn from more than a decade of shifts.
In looking at everything from early beginnings of rudimentary worm-based attacks to the now commonplace and sophisticated attacks that leverage weaknesses in the foundation of trust, it has become apparent that state-backed and organized cybercriminals learned from early hackers that they could use their vast resources for a variety of nefarious, disruptive and lucrative activities by simply developing heavy-hitting advanced cyber weaponry. We also learned that many of the cyberweapons developed by well-backed players and nation states became templates for attacks that have made their way onto the digital streets, and are now available to lone-wolf hackers and highly organized cybercrime syndicates.
Every era of cyberattacks we looked at was characterized and defined by the attackers’ unique goals and methods. Black Hat began in 1997, about the same time that hackers looking for fame–and looking to disrupt computer systems–were launching cyberattacks via worms and viruses. The mid to late 2000s saw the emergence of spyware and bots launched by cybercriminals in search of financial gain. In more recent years, we’ve seen a growing trend in hacktivism, as individuals and groups look to make political statements by launching Distributed Denial of Service (DDoS) attacks against the websites of particular groups and companies.
The most recent era has proven to be the most dangerous yet, as attacks are no longer launched by just the lone wolves of the world. Joining the fray are heavily-backed cybercriminals and state-backed actors with political and financial motives. Having reaped the rewards of early methods, these new players have developed and are now launching multi-stage advanced, targeted and persistent attacks that have national security implications and cost organizations billions of dollars every year. These attacks take advantage of weaknesses in the foundations of digital security and leverage targets’ poor practices when it comes to controlling basic technologies such as cryptographic keys and digital certificates, which are designed to ensure trust.
Advanced attack techniques are now readily available to everyone, including common cybercriminals. Because the attacks have been templatized and placed in the hands of the masses, nearly anyone with a cause and dedication can launch one that will erode the foundations of security and trust. Any organization with valuable information to protect has to worry about attacks being launched from both grandma’s basement and from facilities identified by the likes of Mandiant.
What can the modern enterprise do?
The intelligence trends we uncovered demonstrate that organizations can mount an effective cyberdefense. Security and risk professionals need to understand that the means by which digital smart weapons are guided into their targets and authenticate within target networks have changed dramatically.
The chart below highlights the evolution of cyberattacks since 1997, the year Black Hat launched. As IT has expanded, so too have the type and variety of attacks. This has forced organizations to contend with diminished trust, a problem driven largely by the failure to secure and protect certificates and keys.
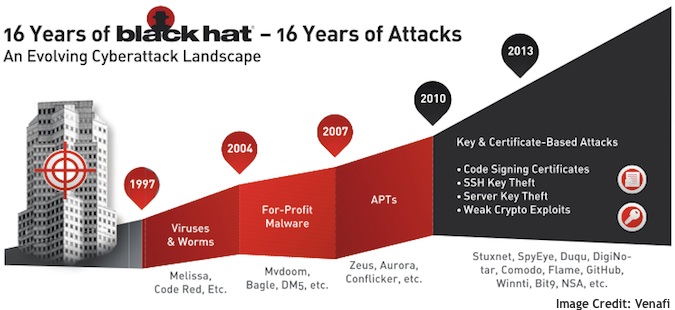
As the graphic shows, the past 16 years have presented the IT security industry with some extreme challenges and powerful learning opportunities. While our research reveals many of these, some of the most salient warnings for enterprises and governments include the following:
• Attacks are gaining deep and undetected access to global enterprise and government networks
• Credentials, intellectual property, state secrets, and corporate and consumer data are being stolen in unquantifiable volumes
• Systems and computers are infected with dynamic malware that conducts automated cyberespionage and data theft
• Attacks and malware can be used to destroy industrial facilities
• Heavily backed cybercriminals have reaped the fruits of earlier attacks and used their resources to take advantage of cryptographic keys and digital certificates to bore through IT security foundations
• Just as military weapons have made their way into criminal communities, so to have advanced cyberattack techniques that leverage keys and certificates made their way into all levels of the cybercriminal community
Knowing the evolution of cybercrime is half the battle. Every organization needs to take steps to keep its networks, data, customers, and keys and certificates safe. You can take three key steps to protect against modern threats and attacks on trust:
1. Gain visibility: The first step in mitigating these trust-based attacks—attacks that use your trusted keys and certificates against you—is to understand your key and certificate inventory. Without clear visibility into the cryptographic credential inventory, strong control over the number and types of keys and certificates, and clear policies assigning owners to particular cryptographic credentials, an organization can do little to defend itself against this latest era of attacks.
2. Monitor for anomalies: Network monitoring tools can help you detect the use of suspicious SSL certificates or SSH sessions in your network. By cross-referencing a suspicious SSL certificate with the known certificate inventory, you can quickly determine whether the SSL traffic is legitimate or possibly part of a targeted attack. Using similar methods, you can also detect suspicious SSH sessions that might indicate a hacker is quietly expanding into your critical systems.
3. Respond quickly: In the event that you detect an anomaly and prove it is malicious, you must respond quickly, limiting the scope of the damage by removing compromised credentials and replacing them with new, valid keys and certificates. Because improper removal of a certificate may impact applications’ trust chains and cause an outage, you must carefully plan and monitor the rotation of any key material. Automated deployment and verification tools not only speed the response but also prevent unexpected downtime due to human errors.















