Everybody’s talking Zero Trust, but it’s not a pre-packaged solution you can buy off the shelf and each organization’s approach will be different. In fact, you may already have the basics in place. For most, it’s a multi-year journey that starts with secure access for all users, devices and workloads.
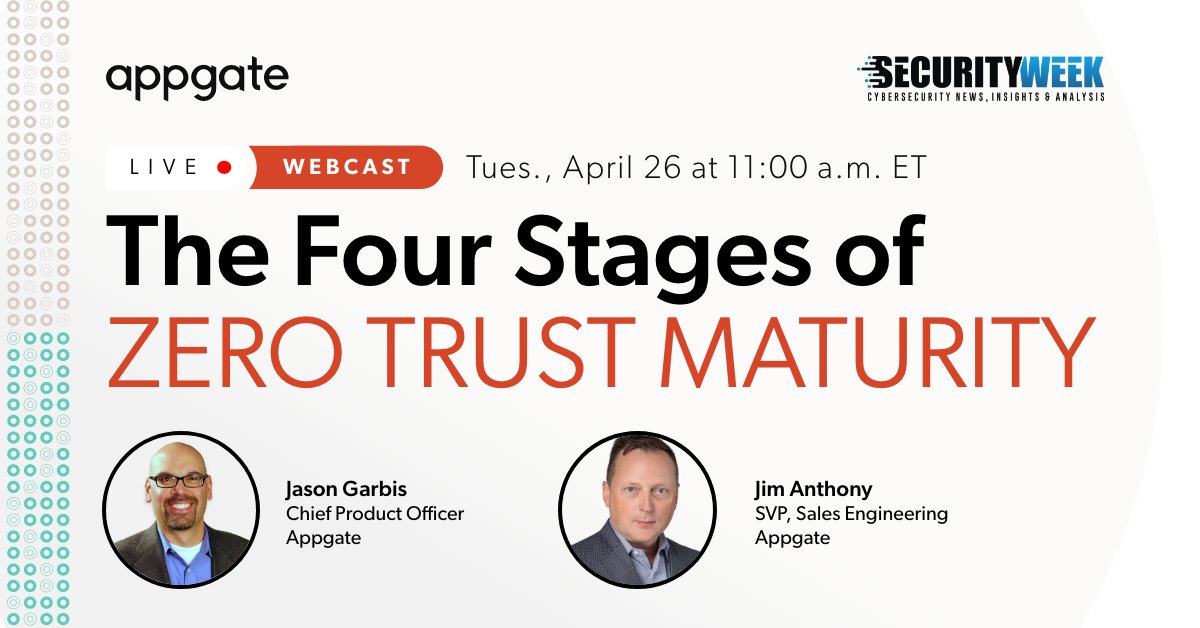
Join this session on the four stages of Zero Trust maturity and how to get fast wins while working toward fully adaptive, context- and risk-aware Zero Trust baked into your IT, security and business ecosystems.
Watch the webcast (now available on demand) that will cover:
Stage Zero: Identify where you are and where to start your Zero Trust journey
Stage One: Put basic Zero Trust principles in place to show immediate value
Stage Two: Leverage context and risk to enhance security posture
Stage Three: Unlock the potential of adaptive Zero Trust