The US cybersecurity agency CISA on Thursday informed organizations about threat actors targeting improperly configured Cisco devices.
The agency has observed malicious hackers acquiring system configuration files by abusing available protocols or software, such as the legacy Cisco Smart Install (SMI) feature.
This feature has been abused for years to take control of Cisco switches and this is not the first warning issued by the US government.
“CISA also continues to see weak password types used on Cisco network devices,” the agency noted on Thursday. “A Cisco password type is the type of algorithm used to secure a Cisco device’s password within a system configuration file. The use of weak password types enables password cracking attacks.”
“Once access is gained a threat actor would be able to access system configuration files easily. Access to these configuration files and system passwords can enable malicious cyber actors to compromise victim networks,” it added.
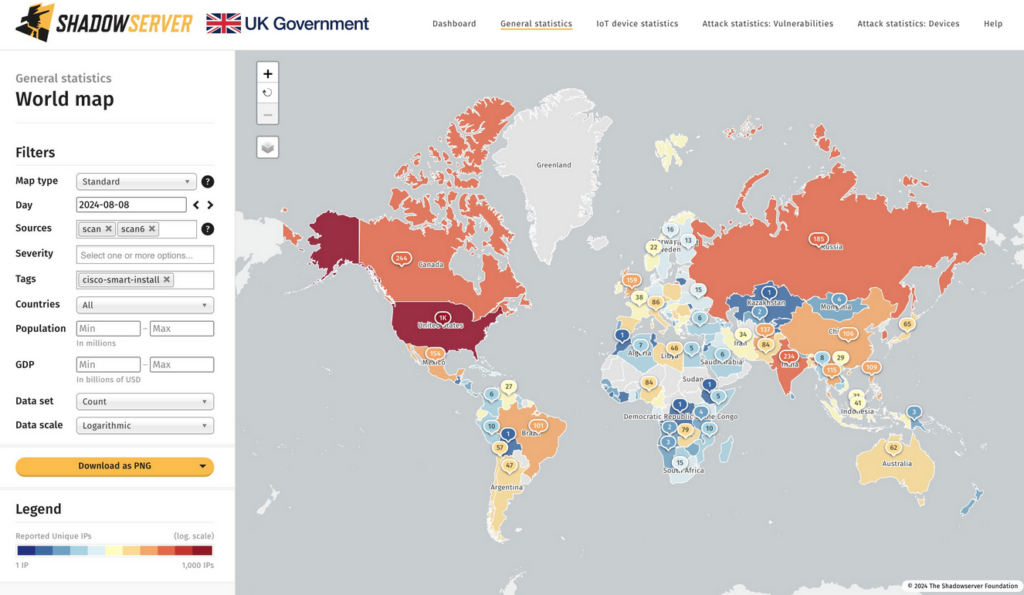
After CISA published its alert, the non-profit cybersecurity organization The Shadowserver Foundation reported seeing over 6,000 IPs with the Cisco SMI feature exposed to the internet.
On Wednesday, Cisco informed customers about three critical- and two high-severity vulnerabilities found in Small Business SPA300 and SPA500 series IP phones.
The flaws can allow an attacker to execute arbitrary commands on the underlying operating system or cause a DoS condition.
While the vulnerabilities can pose a serious risk to organizations due to the fact that they can be exploited remotely without authentication, Cisco is not releasing patches because the products have reached end of life.
Also on Wednesday, the networking giant told customers that a proof-of-concept (PoC) exploit has been made available for a critical Smart Software Manager On-Prem vulnerability — tracked as CVE-2024-20419 — that can be exploited remotely and without authentication to change user passwords.
Shadowserver reported seeing only 40 instances on the internet that are impacted by CVE-2024-20419.
Related: Cisco Patches NX-OS Zero-Day Exploited by Chinese Cyberspies
Related: Cisco Patches Critical Vulnerabilities in Secure Email Gateway, SSM
Related: Cisco Patches Webex Bugs Following Exposure of German Government Meetings


