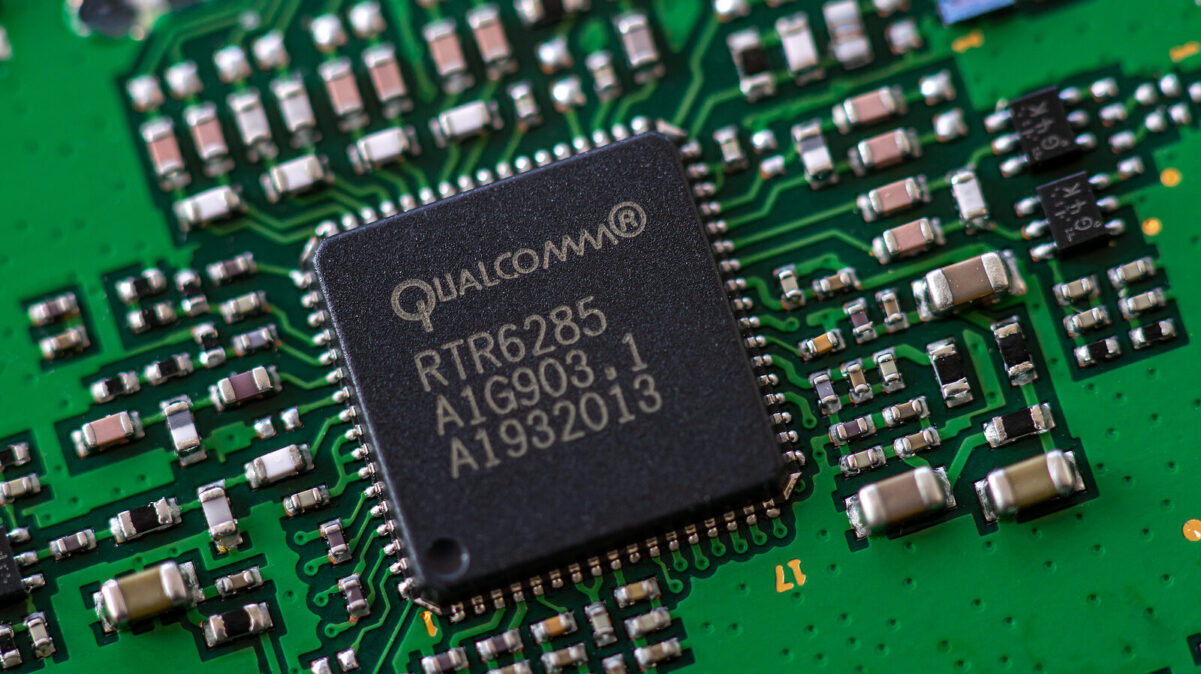
Chip makers Qualcomm and Mediatek on Monday announced patches for many vulnerabilities, including five issues that were resolved with the latest Android fixes.
Qualcomm’s March 2025 security bulletin details 14 security defects impacting proprietary software used in tens of chipset models, including seven issues rated ‘critical severity’.
All critical flaws are described as memory corruption issues. According to Qualcomm, six of them impact the Automotive Software platform based on QNX, while the seventh affects Automotive Vehicle Networks.
The company also announced fixes for five high-severity bugs that could lead to information disclosure, denial-of-service (DoS), and memory corruption. Two medium-severity defects were also resolved.
Additionally, the chip maker rolled out fixes for seven high-severity and six medium-severity flaws in open source components.
“Patches are being actively shared with OEMs, who have been notified and strongly recommended to deploy those patches on released devices as soon as possible,” Qualcomm notes.
Three of the CVEs, namely CVE-2024-43051, CVE-2024-53011, and CVE-2024-53025, were also addressed with the March 2025 Android update.
Mediatek on Monday published information on 10 vulnerabilities affecting dozens of chipsets. Fixes were released for three high-severity issues, including a memory corruption in modems that could lead to DoS, and two out-of-bounds write bugs in KeyInstall and WLAN that could lead to escalation of privileges.
Patches for the modem and KeyInstall flaws, tracked as CVE-2025-20644 and CVE-2025-20645, were also included in this month’s Android updates.
The remaining seven issues that Mediatek resolved this month are medium-severity bugs that could lead to DoS, information disclosure, and escalation of privilege.
According to the company, “device OEMs have been notified of all the issues and the corresponding security patches for at least two months before publication.”
Neither Qualcomm nor Mediatek mentioned any of these vulnerabilities being exploited in the wild.
Related: Qualcomm Extends Security Support for Android Devices to 8 Years
Related: Qualcomm Alerted to Possible Zero-Day Exploited in Targeted Attacks
Related: AI Data Exposed to ‘LeftoverLocals’ Attack via Vulnerable AMD, Apple, Qualcomm GPUs
Related: ‘5Ghoul’ Vulnerabilities Haunt Qualcomm, MediaTek 5G Modems