Chronicle-owned VirusTotal this week announced VirusTotal Collections, a new resource aimed at making it easier for security researchers to share Indicators of Compromise (IoCs).
Collections, the online malware analysis service explains, are live reports that contain, alongside a title and an optional description, a group of IoCs such as domain addresses, file hashes, IPs, and URLs, which can be enhanced with VirusTotal analysis metadata.
Registered VirusTotal users have access to these collections, and their owners can easily add or remove IoCs to/from them, to ensure they remain relevant.
With Collections, VirusTotal aims to eliminate the need for security researchers to use other services, such as Pastebin or other sharing platforms, to make IoCs available to the community.
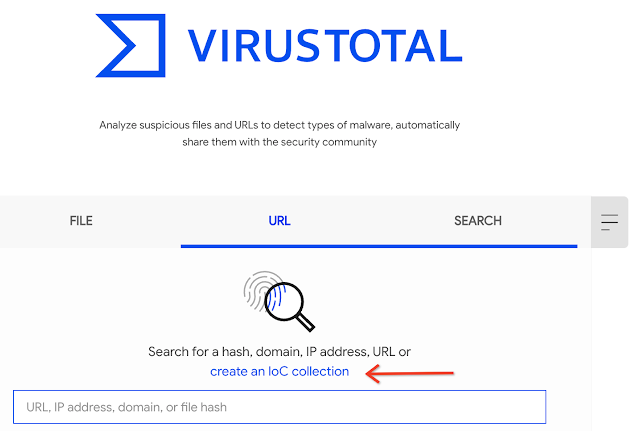
IoC collections can be created by accessing the Search tab from the VirusTotal home page.
VirusTotal Collections, the malware scanning service says, offers a more actionable and contextualized alternative to sharing IoCs, as they are public via the platform’s UI and API, and can be shared using their permalink in blog posts, reports, and the like.
“All our community generated content, including comments, graphs and collections will contribute to the Community section of file, URL, domain and IP address reports. This means that if a security researcher creates a Collection with a file in it, if you visit the file report you will see the collection in the community section,” VirusTotal explains.
Related: VirusTotal Shares Analysis of 80 Million Ransomware Samples
















