Threat actors are impersonating various US government departments in phishing attacks targeting the Microsoft 365 credentials of government contractors.
Since at least mid-2019, the attackers have been observed sending phishing messages spoofing the US Departments of Commerce, Labor, or Transportation to target organizations in various sectors, with a focus on energy and professional services, including construction.
These targeted emails, which claim to request bids for government projects, are well crafted and very convincing, and were seen bypassing protections offered by secure email gateways (SEGs).
According to phishing prevention and detection firm Cofense, the phishing campaigns have evolved with improved emails and lure PDFs, as well as with updated appearance and behavior of the employed phishing pages.
Some of the most recent attacks have been spoofing .gov email addresses, using logos, consistent formatting, signature blocks, and detailed instructions to increase their sense of legitimacy. The attackers also switched from sending the lure PDF as an attachment to including a link to the document.
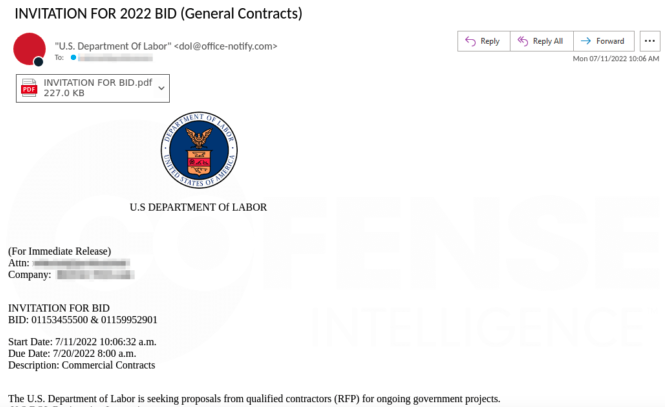
The recently observed lure PDFs are featuring the logo of the spoofed government department on the first page, with details about an alleged bidding process placed on the second page, along with the lure to clicking an included link.
The documents also provide more information relevant to the victim, and feature customized metadata that closely resembles that associated with an authentic invitation-for-bid toolkit PDF, Cofense says.
Once the victim clicks on the phishing link in the lure document, they are taken to an initial page that mimics the home page of the spoofed government department, but which includes an extra red button encouraging the victim to click it in order to bid.
To increase the legitimacy of the page, the attackers use HTTPS and specifically emulate government-bid-related themes, informing the victim that they should provide Microsoft Office credentials in order to enter the bidding. A captcha is also served to the victim.
After the credentials are exfiltrated, the victims are redirected to the relevant government department’s legitimate webpage, with no hint whether they have successfully completed the bidding process. However, the lure PDFs specifically instruct the victims not to submit their credentials twice.
“These campaigns are convincing from start to finish and make use of preexisting data copied from legitimate sources in order to mislead victims. The consistent impersonation of a United States federal department is carried out each time with updated information including watermarks on PDFs and information on the credential phishing pages,” Cofense notes.
Related: Google Blocks Chinese Phishing Campaign Targeting U.S. Government
Related: Microsoft: 10,000 Organizations Targeted in Large-Scale Phishing Campaign
Related: APT Group Using Voice Changing Software in Spear-Phishing Campaign













