Software update and support tools preinstalled on PCs from some of the world’s biggest original equipment manufacturers (OEMs) introduce serious vulnerabilities that expose users to remote attacks.
News broke last year that Dell had been installing a root certificate named eDellRoot on systems via Dell Foundation Services to allow support staff to quickly identify the computer model when providing service to customers. Researchers discovered this security issue just months after Lenovo was caught installing a self-signed root certificate to facilitate a piece of adware dubbed Superfish.
Researchers from Duo Security have now conducted a thorough analysis of the software updaters shipped by several major PC makers, including Acer, Asus, Dell, HP and Lenovo. Experts have analyzed Acer Care Center, Asus Live Update, Dell Update, the update plugin in two versions of Dell Foundation Services (DFS), HP Support Solutions Framework (HPSSF), Lenovo Solutions Center, and Lenovo UpdateAgent.
Duo Security has analyzed these updaters as shipped with Flex 3 and G50-80 devices from Lenovo, Envy and Stream (x360) from HP, Acer Aspire, Inspiron 15 and 15-5548 from Dell, and TP200S from Asus. While experts have found some local privilege escalation vulnerabilities, the research has focused on remote attacks that can be launched by man-in-the-middle (MitM) attackers.
Researchers discovered that each of the tested updaters is plagued by at least one flaw that can be easily exploited to achieve remote code execution with SYSTEM permissions, which can lead to a complete compromise of the vulnerable device. The most common problems were related to the use of TLS, update integrity validation, and verification of the update manifest’s authenticity.
In some cases, experts also discovered that the applications performed silent updates, which could make it easy for attackers to push malicious software without raising any suspicion. While some vendors used encryption to protect configuration files and registry data, Duo Security managed to easily reverse engineer these obfuscation attempts.
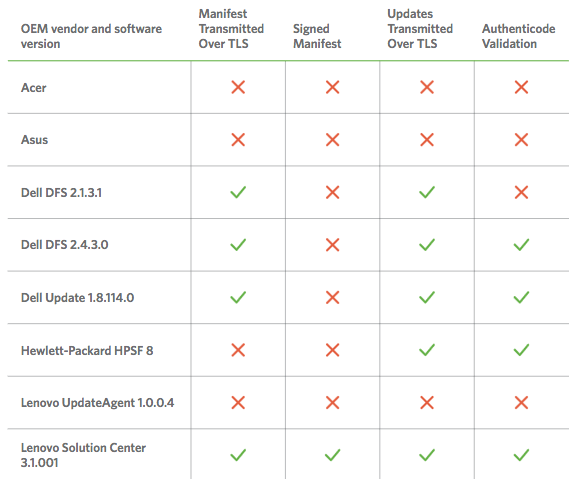
One of the most common issues found by researchers was the lack of TLS. All of Dell’s update tools and Lenovo’s Solution Center leverage HTTPS to transmit manifests, the files used to inform the system of a new package or software update. However, Lenovo’s UpdateAgent and products from Acer, Asus and HP use HTTP.
Lenovo Solution Center is the only application that uses signed manifests. The lack of TLS and integrity validation allows MitM attackers to modify the manifest to prevent users from getting important updates, or they can leverage malicious manifest files to install malware.
In the case of Acer Care Center, Asus Live Update and Lenovo UpdateAgent, an attacker can easily replace legitimate update files with malicious ones because none of these tools use TLS to transmit updates.
Microsoft’s Authenticode allows developers to sign executable files and software packages, but Acer Care Center, Asus Live Update and Lenovo UpdateAgent don’t perform such validation.
Overall, Lenovo’s Solution Center is the most secure, but the company’s UpdateAgent failed all tests, along with products from Acer and Asus.
Researchers identified a total of 12 vulnerabilities across the products from the tested OEMs, with each vendor’s tools being plagued by at least one high-risk flaw.
UPDATE. Lenovo has published an advisory telling users to uninstall Lenovo Accelerator Application from their computers.
Related: HP Support Framework Bug Allows Arbitrary File Downloads, Data Harvesting
Related: Samsung Fixes MiTM Flaw in Software Update Utility
Related: Lenovo Patches Privilege Escalation Flaws in System Update
Related: Intel Patches Vulnerability in Driver Update Utility







