Palo Alto Networks today released its semi-annual Application Usage and Risk Report, a report that digs into employee activity and the types of applications in use on corporate networks, and what it means for enterprise security.
 The Application Usage report is particularly interesting because it’s generated based on raw data coming from activity happening on enterprise networks, and not through a user-based survey. The data gathered for these reports comes from evaluation units of the company’s Next Generation Firewalls deployed at potential customer locations. This most recent report provides a view into application usage based on traffic coming from more than 1,600 enterprises between April 2011 and November 2011.
The Application Usage report is particularly interesting because it’s generated based on raw data coming from activity happening on enterprise networks, and not through a user-based survey. The data gathered for these reports comes from evaluation units of the company’s Next Generation Firewalls deployed at potential customer locations. This most recent report provides a view into application usage based on traffic coming from more than 1,600 enterprises between April 2011 and November 2011.
The report also analyzes the risks inherent with the growth of application usage at work as well as examines how companies can effectively and securely enable applications at work, ensuring the right levels of productivity with security.
Highlights from the Application Usage Report include:
Traffic Types are Changing: Securing Port 80 Does Not Secure Your Network
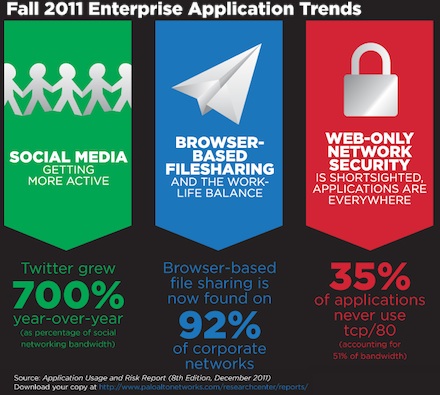
Historically, most of an organization’s network traffic passed through TCP Port 80. But times are changing. The traffic analyzed in the report revealed that 51% of the bandwidth consumed by 35% of the applications is NOT using port 80. In contrast, the 297 applications that use only port 80, and no other port by default, represent just 25% of the applications and 32% of the bandwidth consumed.
In fact, for the first time, applications with traffic crossing port 80 now represent a minority of the traffic on enterprise networks. With this type of network activity, a web browsing-focused security model will not protect much of an organization’s overall traffic.
 “If [port 80] is the only focus, it’s fairly short-sighted and you’re ignoring a set of business and security risks on the other ports,” Matt Kiel, Senior Threat Analyst at Palo Alto Networks told SecurityWeek.
“If [port 80] is the only focus, it’s fairly short-sighted and you’re ignoring a set of business and security risks on the other ports,” Matt Kiel, Senior Threat Analyst at Palo Alto Networks told SecurityWeek.
“Non-web-based traffic and application use is much more significant than most people think,” Keil said.
Widespread File Sharing Poses Increased Threat
The use of browser-based file sharing applications from companies such as Box.net and Dropbox grew in popularity in the workplace, with the report showing that 92 percent of organizations have such applications in use on their networks.
In total, 65 different browser-based file-sharing variants were found with an average of 13 being used in each of the analyzed organizations. The use of evasive techniques by these applications implies that they are often operating unchecked on corporate networks, the report explains.
Social Networking Application Usage Spikes
The report revealed explosive growth in global social networking and browser-based file sharing on corporate networks, citing a 300 percent increase in active social networking compared with activity during the same period in 2010.
Twitter bandwidth consumption at work grew by more than 700 percent year-over-year: from three percent in October 2010 to 21 percent in December 2011.
“Whether or not employees are using social networks or sharing files at work is no longer a question; this data clearly demonstrates that users are embracing and actively using such applications,” said René Bonvanie, chief marketing officer at Palo Alto Networks. “Companies must determine how to safely enable these technologies on their networks so that users can maintain the levels of productivity that many of these applications can afford, while at the same time ensuring that their corporate networks and users are protected against all threats.”

