Exploits targeting Tesla cars, operating systems, and popular software earned participants over $1.1 million at Pwn2Own Vancouver 2024, Trend Micro’s Zero Day Initiative (ZDI) said on Thursday after the event wrapped up.
On the first day, participants earned a total of $732,500 for 19 unique zero-day vulnerabilities found in Tesla cars, Windows, Ubuntu, Oracle VirtualBox, VMware Workstation, Chrome, Edge, and Adobe Reader.
The highest single prize, $200,000, was awarded to the team representing cybersecurity firm Synacktiv, which also received a new Tesla Model 3 for demonstrating an exploit against the car’s electronic control unit (ECU).
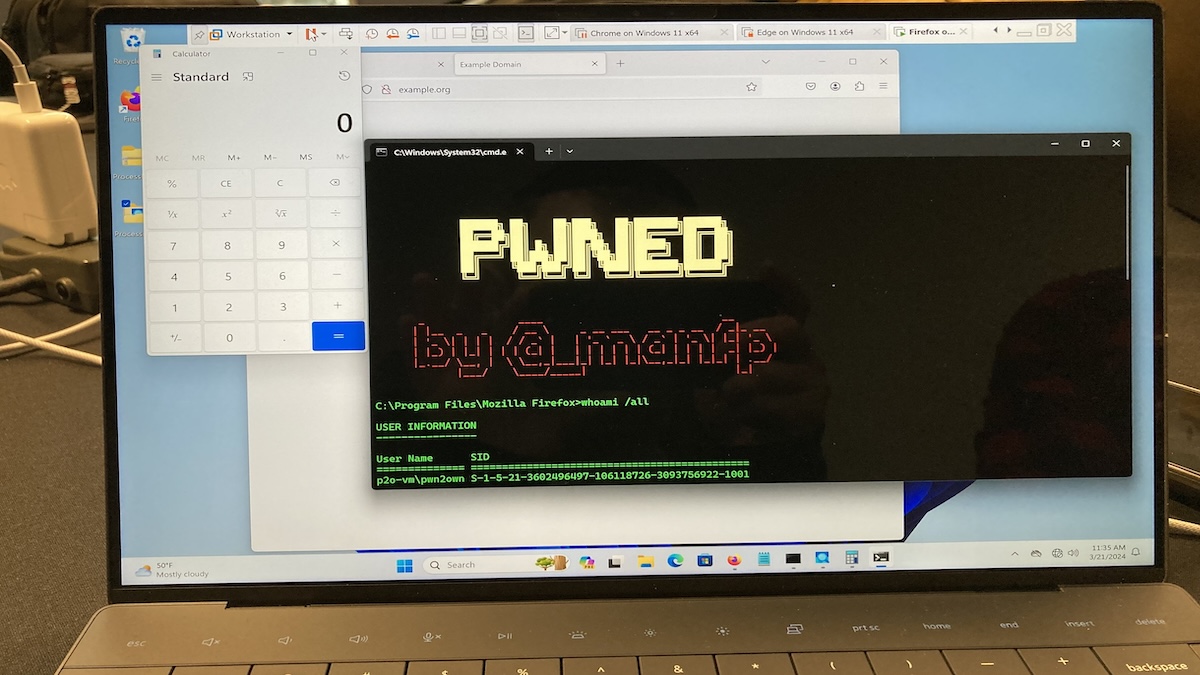
On the second day, the highest reward, $100,000 went to Manfred Paul, for a Firefox exploit that involved remote code execution and a sandbox escape. The researcher was declared the winner of this Pwn2Own, earning a total of more than $200,000 after also hacking the Safari, Chrome and Edge browsers.
Another significant reward, $85,000, was earned on the second day by Seunghyun Lee of Kaist Hacking Lab for a remote code execution exploit affecting both Chrome and Edge.
The only Docker exploit presented at Pwn2Own earned the Star Labs SG team $60,000. The same team also earned $30,000 for a VMware Workstation exploit that involved one previously known vulnerability.
The Palo Alto Networks team received $42,500 for an exploit that works against both Chrome and Edge.
Others earned thousands of dollars for Windows 11, Ubuntu, and Oracle VirtualBox exploits.
A total of 29 unique zero-day vulnerabilities were demonstrated at Pwn2Own Vancouver 2024, earning participants $1,132,500. ZDI said it paid out a total of nearly $3.5 million at the last three Pwn2Own events.
Related: Tesla Hacked Twice at Pwn2Own Exploit Contest
Related: Hackers Earn $1.3M for Tesla, EV Charger, Infotainment Exploits at Pwn2Own Automotive
Related: Hackers Earn Over $1 Million at Pwn2Own Toronto 2023