On Wednesday, CrySyS Lab, the Laboratory of Cryptography and System Security at Budapest University of Technology and Economics, after being notified by the Hungarian National Security Authority (NFB), unveiled details on a near decade-long cyber espionage operation aimed at high profile targets, mainly in Eastern European countries.
Interestingly, the primary attack tool used is a legitimate software product designed to provide remote computer support. In their attacks, the attackers performed their intelligence gathering and surveillance partly using TeamViewer, a tool commonly used for remote administration.
 According to CrySyS, the attackers install a legitimate version of TeamViewer on the victim’s PC, but then modify it using DLL hijacking to gain remote access to the target system.
According to CrySyS, the attackers install a legitimate version of TeamViewer on the victim’s PC, but then modify it using DLL hijacking to gain remote access to the target system.
“The attackers are not only able to remotely observe the infected computers, but they can also misuse TeamViewer to install other tools to obtain important information, files, and other data from the victim,” the technical report explained.
Because of the attacker’s use of TeamView, researchers have named the malicious toolkit ‘TeamSpy‘.
While not as complex as some other recently discovered cyber weapons, TeamSpy joins the ranks of other high profile cyber espionage tools such as Duqu, Flame, Gauss and Red October.
According to CrySys, the ‘TeamSpy’ attack toolkit can search systems for document types including Microsoft Word, Excel, PDFs, .rtf and, files that included the names, *saidumlo* *secret* *секрет*.* *парол*.* *. *.pgp*, and *pass*.
“This list shows the interest of the attackers in “secret” and “password” documents. In addition, the attackers’ interest in .pgp and .p12 files indicates that they were looking not only for passwords, but also for cryptographic keys, which goes beyond attacks against ordinary users,” the report explained.
The attacks appear to be part of a nation-state cyber-surveillance/espionage operation targeting high profile targets throughout Eastern European nations. While the exact targets have not been disclosed by CrySyS, some information on victims show the following organizations were hit:
• 11/2012: Hungarian high profile governmental victim.
• 03/2013: Embassy of NATO/EU state in Russia
• 04/2010: Electronics company in Middle-East, Govt. background
• 03/2013: Multiple research/educational organizations in France and Belgium
• 03/2013: Industrial manufacturer in Russia
According to analysis from Kaspersky Lab, attackers have focused on hitting a variety of targets, ranging from activists and political targets, to heavy industry and national information agencies.
Based on the samples collected so far, CrySyS believes same threat actor produced many individual malware modules over the last ten years, some created solely to steal specific office documents, as mentioned above.
Once installed, attackers can remotely control the TeamSpy malware running on victim computers using the TeamViewer application (teamviewer.exe) which runs as a legitimate process.
What’s also interesting, is that according the company’s website, TeamViewer generates a session password that changes with every software start to provide additional security against unauthorized access to a remote system.
However, it seems that the customizations and DLL hijacking by the attackers have overcome TeamViewer’s security measures.
“Also it is not possible to invisibly control a computer,” the TeamViewer website explains. “For data protection reasons the person sitting on the remote computer has to be able to detect when someone is accessing the machine.”
SecurityWeek contacted TeamView, Inc. about the topic but did not recieve a response prior to publication.
Analysis of the command-and-control infrastructure shows that at least one of the domain names was registered in 2004. Interestingly, the attacks were previously brought up by Belarussian activists in a public warning in April 2012.
“During our investigation, we uncovered a large set of malware samples that were probably utilized back in the past; hence, our analysis can also shed light on older malware campaigns and might help victims to reveal incidents that are several years old,” CrySys researchers wrote in a blog post. “Therefore, the information disclosed in this report could be used to perform a longitudinal study of targeted malware attacks.”
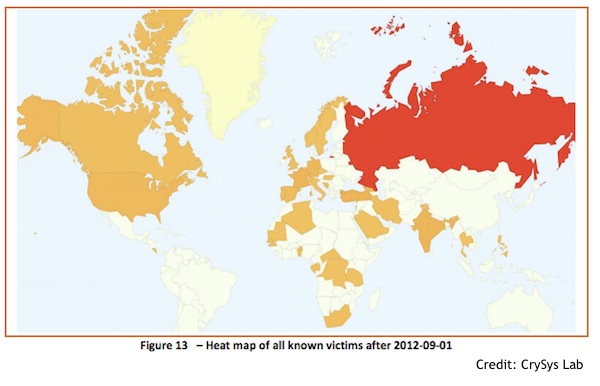
ESET confirmed seeing some of these malicious components around the world in very small quantities over the course of last few years. According to ESET’s data, victims were locations in Turkey, Russia, Ukraine, Italy and a few Middle-East and former USSR countries. ESET also confirmed the existence of more variants of the avicap32.dll file used with TeamViewer, noting that some were recent.
The attackers aim for important targets, the report concluded. “This conclusion comes from a number of different facts, including victim IPs, known activities on some targets, traceroute for probably high profile targets, file names used in information stealing activities, strange paramilitary language of some structures, etc.”
This is a developing story and will be updated as more research is uncovered and analyzed.
Additional Research: CrySys Lab (PDF)
Additional Research: Kaspersky Lab (PDF)
Additional Research: Symantec – TeamSpy: Backdoor to the Viewer (Blog)
Related Podcast: Ryan Naraine talks to Dr. Boldizar Bencsath of CrySyS Lab and Costin Raiu of Kaspersky Lab about Symantec’s recent Stuxnet 0.5 discovery and the connections to the other cyber-surveillance operations like Duqu and Flame. Listen Now















