Cybersecurity for the software-driven Sentinel nuclear missile has been a top focus of the program
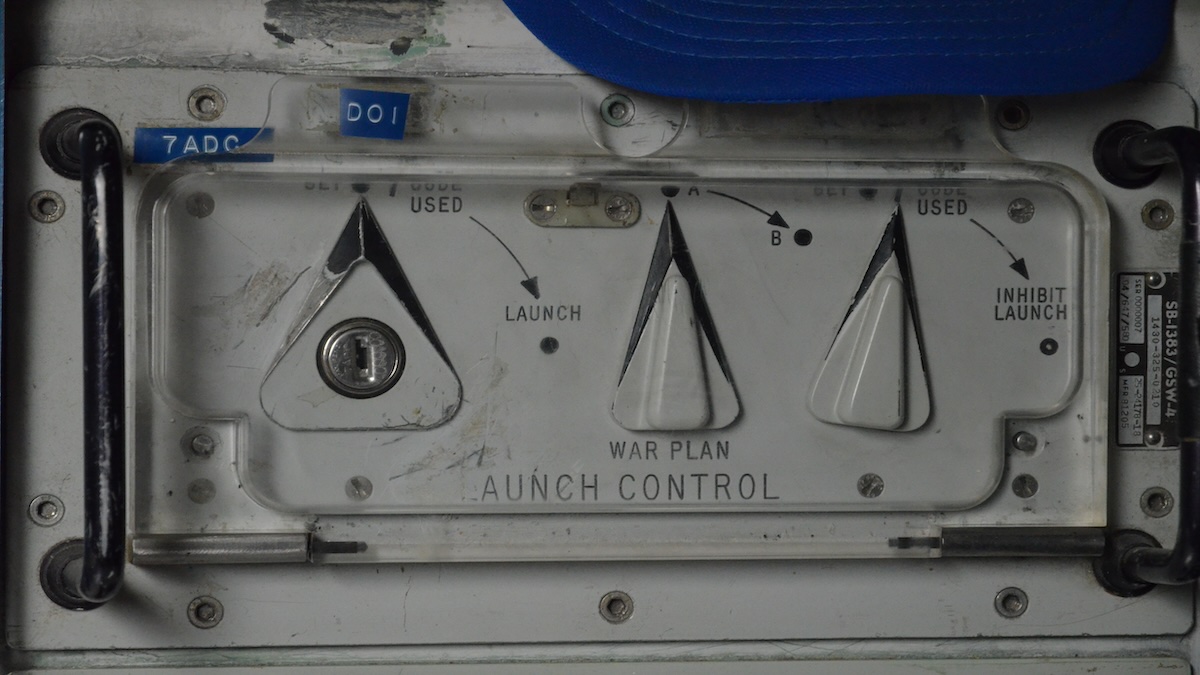
The control stations for America’s nuclear intercontinental ballistic missiles have a sort of 1980s retro look, with computing panels in sea foam green, bad lighting and chunky control switches, including a critical one that says “launch.”
Those underground capsules are about to be demolished and the missile silos they control will be completely overhauled. A new nuclear missile is coming, a gigantic ICBM called the Sentinel. It’s the largest cultural shift in the land leg of the Air Force’s nuclear missile mission in 60 years.
But there are questions as to whether some of the Cold War-era aspects of the Minuteman missiles that the Sentinel will replace should be changed.
Making the silo-launched missile more modern, with complex software and 21st-century connectivity across a vast network, may also mean it’s more vulnerable. The Sentinel will need to be well protected from cyberattacks, while its technology will have to cope with frigid winter temperatures in the Western states where the silos are located.
The $96 billion Sentinel overhaul involves 450 silos across five states, their control centers, three nuclear missile bases and several other testing facilities. The project is so ambitious it has raised questions as to whether the Air Force can get it all done at once.
An overhaul is needed.
The silos lose power. Their 60-year old massive mechanical parts break down often. Air Force crews guard them using helicopters that can be traced back to the Vietnam War. Commanders hope the modernization of the Sentinel, and of the trucks, gear and living quarters, will help attract and retain young technology-minded service members who are now asked each day to find ways to keep a very old system running.
Nuclear modernization was delayed for years because the United States deferred spending on new missiles, bombers and submarines in order to support the post 9/11 wars overseas. Now everything is getting modernized at once. The Sentinel work is one leg of a larger, nuclear weapons enterprise-wide $750 billion overhaul that is replacing almost every component of U.S. nuclear defenses, including new stealth bombers, submarines and ICBMs in the country’s largest nuclear weapons program since the Manhattan Project.
For the Sentinel, silo work could be underway by lead contractor Northrop Grumman as soon as 2025. That is 80 years after the U.S. last used nuclear weapons in war, the bombs dropped on Hiroshima and Nagasaki in Japan, which killed an estimated 100,000 in an instant and likely tens of thousands more over time.
For the Pentagon, there are expectations the modern Sentinel will meet threats from rapidly evolving Chinese and Russian missile systems. The Sentinel is expected to stay in service through 2075, so designers are taking an approach that will make it easier to upgrade with new technologies in the coming years. But that’s not without risk.
“Sentinel is a software-intensive program with a compressed schedule,” the Government Accountability Office reported this summer. “Software development is a high risk due to its scale and complexity and unique requirements of the nuclear deterrence mission.”
Air Force Secretary Frank Kendall has acknowledged the challenges the program is facing.
“It’s been a long time since we did an ICBM,” Kendall said in November at a Center for New American Security event in Washington. It’s “the biggest thing, in some ways, that the Air Force has ever taken on.”
“Sentinel, I think quite honestly, is struggling a little bit,” he said.
New Connections
By far, the biggest cultural shift the Sentinel will bring is the connectivity for all those who secure, maintain, operate and support the system. The overhaul touches almost everything, even including new equipment for military chefs who cook for the missile teams. The changes could improve efficiency and quality of life on the bases but may also create vulnerabilities that the analog Minuteman missiles have never faced.
Since the first silo-based Minuteman went on alert at Montana’s Malmstrom Air Force Base on Oct. 27, 1962 — the day Cuba shot down a U-2 spy plane at the height of the Cuban missile crisis — the missile has “talked” to its operators through thousands of miles of hard-wiring in cables buried underground.
Those Hardened Intersite Cable Systems, or HICS, cables carry messages back and forth from the missile to the missileer, who receives those messages through a relatively new part of the capsule — a firing control console called REACT, for Rapid Execution and Combat Targeting, that was installed in the mid-1990s.
It’s a closed communication loop, and a very secure one that brings its own headaches. Any time the Air Force wants to test one of the missiles, it literally has to dig up the cables and splice them, to isolate that test missile’s wiring from the rest. Over decades of testing, there are now hundreds of splices in those critical loops.
But it’s also one of the Minuteman’s best features. You would need a shovel — and a lot more — to try to hack the system. Even when missile crews update targeting codes, it is a mechanical, manual process.
Minuteman is “a very cyber-resilient platform,” said Col. Charles Clegg, the Sentinel system program manager.
Clegg said cybersecurity for the software-driven Sentinel has been a top focus of the program, one that has all of their attention.
“Like Minuteman, Sentinel will still operate within a closed network. However, to provide defense in depth, we will have additional security measures at the boundary and inside the network, enabling our weapon system to operate effectively in a cyber-contested environment,” Clegg said.
Frigid Fields
Those who maintain the Minuteman III have tried over the years to bring in new technology to make maintenance more efficient, but they have found that sometimes the old manual way of tracking things — sometimes literally with a binder and pen — is better, especially in frigid temperatures.
Nuclear missile fields are located in Colorado, Montana, Nebraska, North Dakota and Wyoming. Those missiles need maintenance even in the winter, and crews spend hours outside in sub-zero field conditions,
“An iPad won’t survive a Montana winter” at the launch sites, where maintenance crews have worked outdoors in temperatures of minus 20 degrees or even minus 40 degrees, said Chief Master Sgt. Virgil Castro, the 741st missile maintenance squadron’s senior enlisted leader.
Also, when maintenance crews at Malmstrom tested some radio frequency identification, or RFID, technology — think of how seaports track items inside cargo containers — it created security vulnerabilities.
“Today, everything is connected to the internet of things. And you might have a back door in there you don’t even know” said Lt. Col. Todd Yehle, the 741st maintenance squadron commander. “With the old analog systems, you’re not hacking those systems.”
What it means is that even though technology could automate the whole operations process, one critical aspect of missile launch will remain the same. If the day comes that another nuclear weapon must be fired, it will still be teams of missileers validating the orders and activating a launch.
“It’s the human in the loop,” said Col. Johnny Galbert, commander of the 90th Missile Wing at F.E. Warren. “I think what it comes down to is we want to rely on our airmen, our young officers out there, to make that decision, to be able to interpret what higher headquarters is telling them or directing them to do.”