Organizations using certain Logix programmable logic controllers (PLCs) made by Rockwell Automation have been informed about a high-severity security bypass vulnerability discovered by researchers at industrial cybersecurity firm Claroty.
On August 1, Claroty published a blog post describing its findings, and Rockwell and the cybersecurity agency CISA published advisories for the flaw, which is tracked as CVE-2024-6242.
The vulnerability was found in Rockwell Automation’s ControlLogix 1756 devices, but the vendor determined that GuardLogix and other controllers are impacted as well. Patches have been released for each supported product and mitigations are also available.
“A vulnerability exists in the affected products that allows a threat actor to bypass the Trusted Slot feature in a ControlLogix controller,” Rockwell said in its advisory. “If exploited on any affected module in a 1756 chassis, a threat actor could potentially execute CIP commands that modify user projects and/or device configuration on a Logix controller in the chassis.”
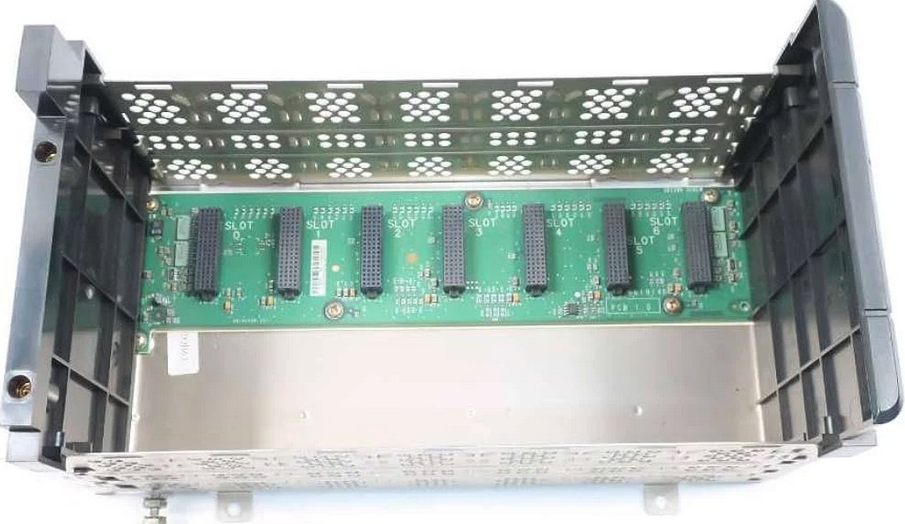
According to Claroty, the attack it has devised involves the 1756 chassis, which is an enclosure that houses I/O modules, communication processors and controllers, and which provides the connections necessary for the interoperation of these components.
The attack also involves the common industrial protocol (CIP) used by 1756 PLCs for communication, and the backplane, which is the printed circuit board that connects the slots (aka modules or cards) within the chassis.
Claroty discovered a vulnerability in a chassis security feature named ‘trusted slot’, which is designed to block communications from untrusted network cards.
“We found a vulnerability that allowed an attacker to bypass the trusted slot feature, jumping between local backplane slots within a 1756 chassis using CIP routing, traversing the security boundary meant to protect the CPU from untrusted cards,” Claroty explained.
“An attacker with this kind of access would be able to send elevated commands such as downloading logic to the PLC CPU even if the attacker is located behind an untrusted network card,” it added.
While the vulnerability could have serious implications, the cybersecurity firm noted that exploitation requires network access to the targeted device.
Learn More at SecurityWeek’s ICS Cybersecurity Conference
The leading global conference series for Operations, Control Systems and OT/IT Security professionals to connect on SCADA, DCS PLC and field controller cybersecurity.
October 21-24, 2024 | Atlanta
www.icscybersecurityconference.com
Related: APT Exploit Targeting Rockwell Automation Flaws Threatens Critical Infrastructure
Related: Rockwell Automation Patches High-Severity Vulnerabilities in FactoryTalk View SE
Related: Organizations Informed of 10 Vulnerabilities in Rockwell Automation Products

