Security updates released by Adobe on Wednesday for Flash Player patch two vulnerabilities, including a critical flaw exploited by a sophisticated threat actor in attacks aimed at a healthcare organization associated with the Russian presidential administration. The attack may be related to the recent Kerch Strait incident involving Russia and Ukraine.
Adobe’s advisory reveals that the exploited vulnerability, CVE-2018-15982, is a use-after-free bug that allows arbitrary code execution. The issue was patched with the release of Flash Player 32.0.0.101 for Windows, macOS, Linux and Chrome OS. The company has warned users that exploits exist in the wild, but has not shared any details.
Adobe has credited three teams – one working for Gigamon and two teams from Chinese cybersecurity firm Qihoo 360 – and one independent researcher for informing it of the vulnerability.
The Qihoo 360 teams have published several blog posts, written in both English and Chinese, describing the zero-day vulnerability and the attacks involving the exploit. Gigamon has also published a blog post describing the flaw and the attack.
According to experts, the Flash zero-day exploit has been used in an operation aimed at the FSBI “Polyclinic No. 2” of the Administrative Directorate of the President of the Russian Federation. The attackers, which Qihoo 360 researchers described as an advanced persistent threat (APT), delivered the exploit inside a RAR archive containing a specially crafted document.
When opened, the document shows a questionnaire for staff of the Moscow-based hospital. However, in the background, malicious commands are executed by leveraging CVE-2018-15982, and a piece of malware is deployed on the system.
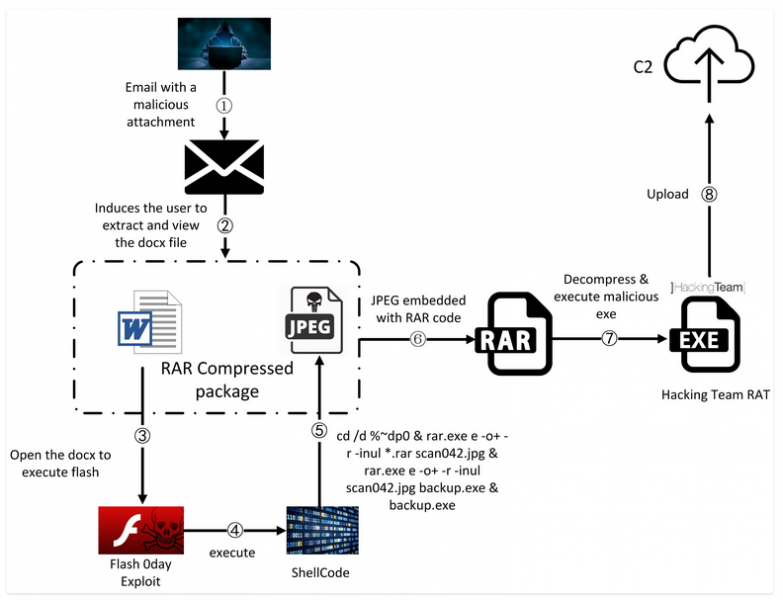
Researchers said the malware is similar to a Trojan from Hacking Team, an Italian spyware maker whose tools were leaked in 2015 following a data breach. The malware used in this attack appears to be a variant of Hacking Team’s Scout tool, said Gigamon.
The Chinese experts noted that the Flash vulnerability is very similar to CVE-2018-4878, which was first exploited by North Korea-linked hackers earlier this year.
Qihoo 360 researchers spotted the attacks on November 29 and reported the vulnerability to Adobe the next day. Gigamon informed Adobe of the flaw on November 29.
Qihoo 360 pointed out that the attack was launched just days after the Kerch Strait incident, which made headlines around the world. On November 25, Russian border guards opened fire on three Ukrainian vessels that had attempted to pass from the Black Sea into the Sea of Azon through the Kerch Strait on their way to the port of Mariupol. The Ukrainian vessels and their 24 crew members were captured.
The media reported that three of the captured crew members were taken to hospitals in Moscow. It is possible that “Polyclinic No. 2” is one of those hospitals and the attackers were seeking information on the captured Ukrainians.
Gigamon said the malicious document analyzed by its researchers was uploaded to VirusTotal from a Ukrainian IP address.
Related: Flash Player Update Patches Disclosed Code Execution Flaw













