A Hands-on, First Look at Dome9 Security’s LiteCloud Automated Cloud Security Firewall Management Service
Dome9 Security, a Tel Aviv, Israel-based company that provides cloud security firewall management solutions, today launched Dome9 LiteCloud, a free service that provides centralized firewall management for servers and clouds in virtual private, cloud, collocated, and hosted environments.
 The service, free for an unlimited number of servers, provides GUI-based firewall management for Windows and Linux servers and clouds to help prevent servers from being misconfigured or left unmanaged and exposed to brute force attacks and vulnerable to exploits.
The service, free for an unlimited number of servers, provides GUI-based firewall management for Windows and Linux servers and clouds to help prevent servers from being misconfigured or left unmanaged and exposed to brute force attacks and vulnerable to exploits.
The company said in a statement today, that the service takes 5 minutes to setup and install. Being a curious and tech-savvy tech journalist, I spontaneously decided to test the service myself and see if it was as easy to setup as Dome9 claimed. So what was originally planned to be a general product news piece, has unexpectedly turned into a review.
To conduct my test, I setup a virtual server equipped with a web server and other typical Linux server services. I quickly signed up for an account with Dome9’s LiteCloud service and followed the instructions. A few command lines was all it took to download and install the server agent used to communicate with Dome9’s management platform. From there, I entered a unique code into the SSH command line interface, and immediately in my web browser I saw that the Dome9 platform had recognized my server and was communicating with it.
So then it was time to see if the service was actually working. In order to see if the service was working, and actually enabling firewall services, I tested out a few rules.
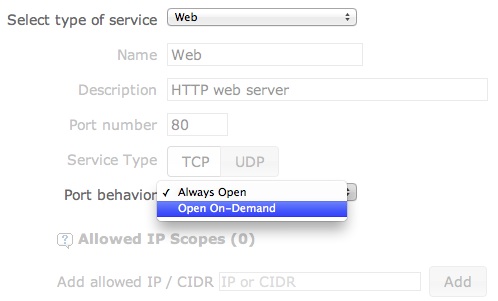 First, I tried to access the default web page that was set to serve on my test server. The page served up quickly as expected. I then made a change via the Dome9 web-based interface to only allow traffic on demand to the HTTP Web Server running on Port 80, changing it from “Always Open” which would allow any connection from any host to the HTTP server. I made the change, clicked “Save” and went back to my other Browser window to test if my server had been locked down. I clicked “Refresh” on the default Web page running on my test server and….nothing. The Browser was unable to connect to the host and nothing served up. The policy worked!
First, I tried to access the default web page that was set to serve on my test server. The page served up quickly as expected. I then made a change via the Dome9 web-based interface to only allow traffic on demand to the HTTP Web Server running on Port 80, changing it from “Always Open” which would allow any connection from any host to the HTTP server. I made the change, clicked “Save” and went back to my other Browser window to test if my server had been locked down. I clicked “Refresh” on the default Web page running on my test server and….nothing. The Browser was unable to connect to the host and nothing served up. The policy worked!
I wasn’t happy testing just one policy so I worked up another. I did a similar thing with SSH which typically runs on Port 22. I launched my SSH client, logged into the test server remotely and all was good. I disconnected from my host while I implemented the policy to block SSH traffic. Once I made the change in the Dome9 interface, I re-launched my SSH client and attempted to tunnel in via SSH to my test server. No success, that policy had worked as well and I was unable to connect to the server. I did the same thing with FTP, but you get the picture.
The Dome9 platform allows admins to create different groups, with different policies and add servers to those groups accordingly. Servers can also be members of more than one group.
The free service includes the ability to have three (3) administrators, and includes features such as activity logging (free edition keeps logs for 30 days), auditing, and support for multiple administrators. Of course with just about any free offering, the company hopes that someday you’ll be a candidate for their paid service. In this case, the company has Dome9’s Business Cloud service, which offers expanded capabilities, including longer log retention, unlimited administrators, access to an API to automate and orchestrate security policies, and a number of other more advanced controls. You can see a feature comparison here.
The platform has a helpful feature that lets administrators grant temporary access for a set period of time, after which the policy will be able to go back into place and close off access. For example, if you maintain a site and have a developer that does maintenance work now and then, you can go in and grant temporary FTP access for just his or her IP (or all IPs) for a set period of time, say an hour or so, while they upload files. After that, without having to worry about changing any settings, the service communicates back to your server and shuts off FTP access again. That feature is part of a premium version, but included for CloudLite users free for 30 days.
For small shops or developers who don’t have dedicated security resources on hand, the service is a great solution to help bring added protection to servers in an easy fashion. For those who manage IP tables through a command line, you’ll find Dome9’s solution to be an easy alternative. And for those looking for more features and controls, the paid version of Dome9’s Business Cloud is priced at 4 cents per hour per server.

